What is Zero Trust Network Architecture (ZTNA)?
Network World
DECEMBER 22, 2022
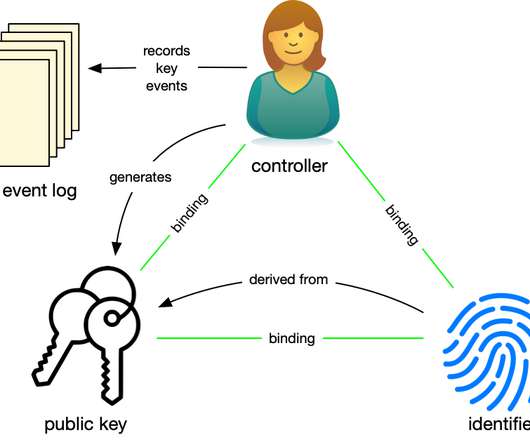
Zero Trust is a term coined by John Kindervag while he was an analyst at Forrester Research to describe a strategic framework in which nothing on the network is trusted by default – not devices, not end users, not processes. Everything must be authenticated, authorized, verified and continuously monitored.

















































Let's personalize your content