What is Zero Trust Network Architecture (ZTNA)?
Network World
DECEMBER 22, 2022
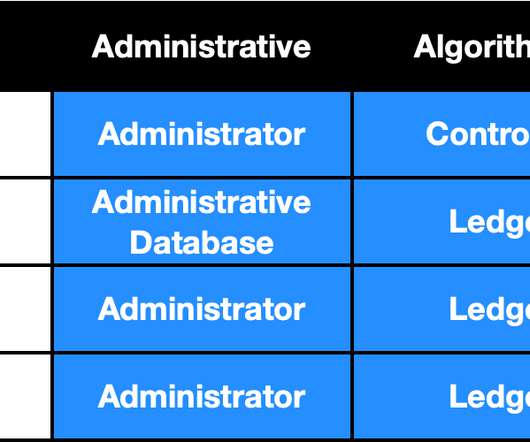
Everything must be authenticated, authorized, verified and continuously monitored. The traditional approach to security was based on the concept of “trust, but verify.” A Zero Trust architecture doesn’t aim to make a system trusted or secure, but rather to eliminate the concept of trust altogether.













































Let's personalize your content