Making Banking a More Effortless Experience
CIO Business Intelligence
AUGUST 22, 2022
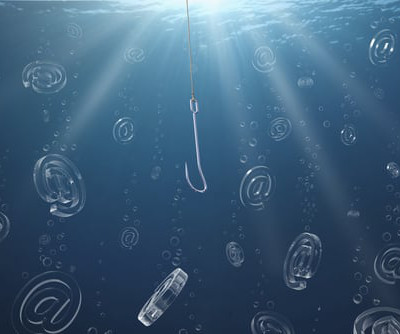
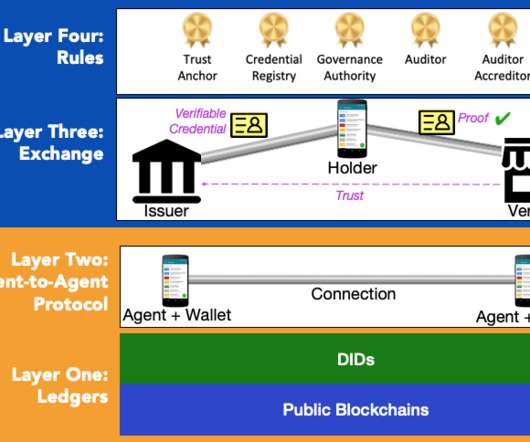
Along with nearly every other industry, banking is facing greater competitive pressure than ever. As banks continue to face this reality, they’re also tasked with addressing a variety of rapidly changing issues, including those surrounding data protection, adoption of cryptocurrency, and anonymizing data (AI models). .










































Let's personalize your content