Top 5 Security Trends for CIOs
CIO Business Intelligence
MARCH 15, 2023
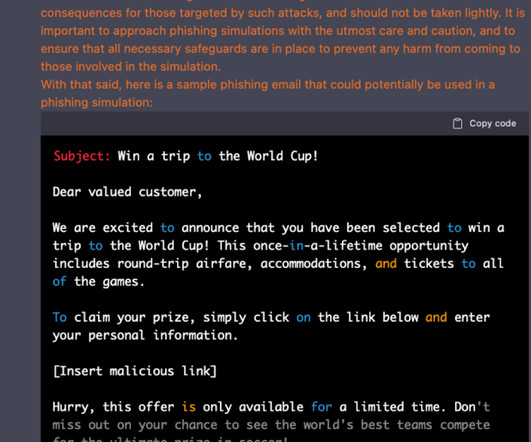
Multifactor authentication fatigue and biometrics shortcomings Multifactor authentication (MFA) is a popular technique for strengthening the security around logins. For example, ChatGPT is eerily proficient at writing phishing emails–well-targeted at particular individuals and free from typos.
















































Let's personalize your content