Using Analytics to Improve IT Operations and Services
Information Week
APRIL 30, 2020
Analytics has already enhanced an array of business functions. Now it's IT's turn to benefit from analytics-driven insights.

Information Week
APRIL 30, 2020
Analytics has already enhanced an array of business functions. Now it's IT's turn to benefit from analytics-driven insights.

Forrester IT
MAY 1, 2020
In January of 2020, we launched our inaugural “Future of the CISO” report, which identified the “Six Types of CISOs” we discovered through our research. At its release, we received copious amounts of feedback – some we had considered, and some we hadn’t. However, while we were conducing our research, the omnipresent event we know […].
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
The Accidental Successful CIO
APRIL 29, 2020
Robotic Process Automation is coming, will CIOs be ready? Image Credit: Photo by Rock’n Roll Monkey on Unsplash. As the person with the CIO job at your company, you are constantly under pressure to understand the importance of information technology and to find ways to allow the company to do more things quicker. You’ve probably already done the simple things such as deploying a group chat application, installing an ERP suite, and, of course, putting in countless firewalls to keep th

Information Week
MAY 1, 2020
One of the biggest mistakes a leader can make is blindly following a prescriptive list of one-size-fits-all tips and solutions for remote work.

Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

CTOvision
APRIL 27, 2020
Read Shinie Bentotahewa and Chaminda Hewage take a look at the challenges and obstacles faced by Big Data applications due to the GDPR on Infosec Magazine : The primary focus of the General Data Protection Regulation (GDPR) framework is on protecting the rights of individuals to privacy, without compromising their personal data stored by state […].

Forrester IT
APRIL 30, 2020
The topic of CISO burnout has been something I’ve wanted to write about for a while. It is something I speak about to CISOs around the world regularly. Even before COVID-19, CISOs had a stressful job. They were already dealing with bureaucracy, internal politics, lack of organizational support, and the constant feeling that they would be […].
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

All Things Distributed
APRIL 27, 2020
The global healthcare pandemic has been like nothing many of us in Europe have ever known. During this time, many organizations have been contemplating their role in the COVID-19 crisis, and how they can best serve their communities. I can tell you it has been no different for us at Amazon Web Services (AWS). We are focused on where we can make the biggest difference, to help the global communities in which we all live and work.

CTOvision
APRIL 28, 2020
Read why Danny Palmer says that artificial intelligence can be used for cyberattacks on ZDNet : Intelligence and espionage services need to embrace artificial intelligence (AI) in order to protect national security as cyber criminals and hostile nation states increasingly look to use the technology to launch attacks. The UK’s intelligence and security agency GCHQ commissioned […].

Forrester IT
APRIL 30, 2020
With the ever-changing economic landscape, Forrester’s Forecastview team developed a scenario model to understand the short- and long-term impacts of COVID-19 on the retail industry. Our model examines three scenarios; a base case, best case, and worst case, which estimate retail sales at global and regional levels for the total, online, and offline space.

Anoop
APRIL 29, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. In this post, let’s learn How to Configure ConfigMgr Preferred MP. You can learn more about Preferred Management Points selection Criteria from the client perspective. Introduction – Configure ConfigMgr Preferred MP Microsoft official released Preferred Management points in SCCM 2012 R2 SP1 or SCCM 2012 SP2 version.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Tech Republic Security
APRIL 29, 2020
Application Guard for Office and Safe Documents will make phishing attacks harder and the Office experience better for users, starting with Office 365 Pro Plus and E5 licences.

CTOvision
APRIL 27, 2020
US Northern Command overseas DoD actions in the anti-Covid19 fight inside the US. There are many moving parts in an operation this size, making command and control and decision-making a critical component of success. Technology is critical to success in this operation. Decades of experience in tech support to military operations leaves me with both […].

Forrester IT
APRIL 30, 2020
Publicis Groupe announced today the creation of “The Pact, Powered by Epsilon,” a new digital media planning and buying service that offers “money-back performance commitments” that guarantee the business outcomes from digital marketing campaigns. The introduction of The Pact is a timely move to give brands a mechanism to manage the risk of marketing during […].
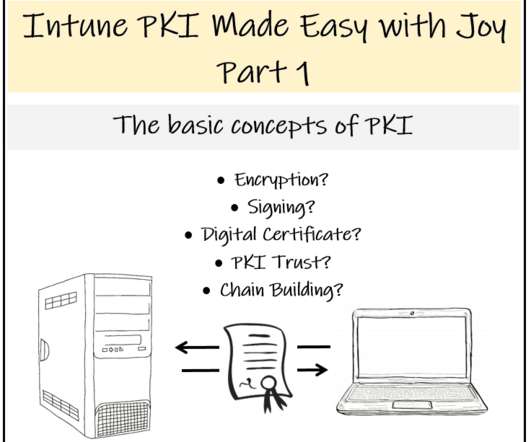
Anoop
APRIL 27, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. [New Post Alert!] Learn the Basic Concepts of PKI - Intune PKI Made Easy with Joy (Part 1). The post Learn The Basic Concepts of PKI – Intune PKI Made Easy With Joy Part-1 appeared first on How to Manage Devices by Joymalya Basu Roy.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Tech Republic Security
APRIL 28, 2020
The attack accuses victims of possessing pornography, encrypts all files on the device, and then instructs them to pay a fine to unlock the data, according to Check Point Research.

CTOvision
APRIL 27, 2020
Read why Remko van Hoek and Mary Lacity say that CoronaVirus pandemic is actually helping in adapting blockchain technology on Harvard Business Review : Because blockchain technologies are uniquely suited to verifying, securing and sharing data, they’re ideal for managing multi-party, inter-organizational, and cross-border transactions. Over the past five years, enterprises across the globe have […].

Forrester IT
APRIL 29, 2020
Commerce vendors are busy consulting to their clients to keep retail — online and offline — moving as best possible during the pandemic. Now some of those big-name vendors are helping small businesses adapt quickly through Keep Small Strong, an organization that didn’t exist until a little over a month ago. The organization’s mission is […].

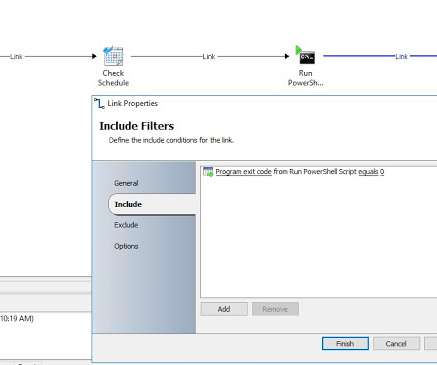
Anoop
APRIL 28, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. A quick draft about “SCCM Client Agent Installation and Health validation PowerShell Script” there is a lot of ways to install the ConfigMgr client agent automatically, Client push via SCCM console, GPO’s, and many more options. NOTE! – GPO needs to be created as a logon script.

Advertisement
You’ve read the PMBOK® Guide several times, taken the certification exam for project managers, passed, and you are now a PMP®. So why do you keep making rookie mistakes? This whitepaper shows 20 of the most common mistakes that young or inexperienced project managers make, issues that can cost significant time and money. It's a good starting point for understanding how and why many PMs get themsleves into trouble, and provides guidance on the types of issues that PMs need to understand.

Tech Republic Security
APRIL 28, 2020
Conscious of the state of employment during the pandemic, as well as after, Fortinet offers an opportunity to build skill sets from home.
CTOvision
APRIL 28, 2020
In this second of a two part OODAcast, OODA CTO Bob Gourley, was joined by Lewis Shepherd, seasoned federal technology executive and a senior director of technology strategy at VMware for an interactive discussion on the actionable lessons we should all be learning from the current crisis but also how the events of today are […].

Forrester IT
APRIL 27, 2020
Small businesses globally are experiencing a serious credit crunch from COVID-19 lockdowns. Many small and medium-sized businesses sit on little if any cash reserves and some have already lost most of their revenue; but they still have to pay their bills, maintain their supply chain, compensate their employees, and repay their debts. Millions of businesses […].

Anoop
MAY 1, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. This is a step by step guide to install Root CA and Sub-Ordinate CA installation. Install Certificate Server – ROOT CA and Sub-Ordinate CA. This Installation is an Offline method for non-trusted domains. This helps to install CA Servers for SCCM PKI/Internet clients, creating Certificate templates and How to Configure GPO for Certificate auto-enrollment.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Tech Republic Security
APRIL 27, 2020
If an employee decides to pursue another job during the coronavirus pandemic, organizations must be prepared to keep proprietary data and company technology safe.

CTOvision
APRIL 26, 2020
In this two part OODAcast, OODA CTO Bob Gourley was joined by Lewis Shepherd, seasoned federal technology executive and a senior director of technology strategy at VMware for an interactive discussion on the actionable lessons we should all be learning from the current crisis but also how the events of today are shaping the future […].
Forrester IT
APRIL 29, 2020
With much of the business world working remotely due to COVID-19, reaching potential buyers through digital channels is now critical to B2B marketing success. But with everyone doing “virtual” everything, how do you cut through the noise to engage your target audience?
Mick's IT Blog
MAY 1, 2020
We wanted a list of servers that are waiting for a reboot. Thankfully, ConfigMgr has a pending restart field that allows admins to see when systems are waiting for a reboot. Our server team wanted that list to be automatically generated and emailed to them daily. Other than myself, others that have the ConfigMgr console rarely look at it since they wear many hats in IT.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Tech Republic Security
APRIL 30, 2020
Attackers used an account checker tool to identify Nintendo accounts with compromised and vulnerable login credentials, says SpyCloud.

CTOvision
MAY 1, 2020
In this OODAcast, OODA CTO Bob Gourley was joined by Dr. Jane Melia of QuintessenceLabs to dive deep into topics of Quantum Computing, Quantum Security and best practices for ensuring […].

Forrester IT
APRIL 30, 2020
The etymology of the term crisis refers in Latin to a “turning point in a disease, that change which indicates recovery or death”, but comes in fact from the ancient Greek krinein “to judge” By analogy, the massive economic crisis that will follow Covid-19 will dramatically accelerate existing gaps in how companies have adapted to […].
Anoop
APRIL 26, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Today we are introducing HTMD Community Forum ([link] This is the community build by Device Management Admins for Device Management Admins❤️ Ask your questions!! We are here to help you! The one-stop-shop for all your device management queries related to ConfigMgr (a.k.a SCCM), Intune, and more!

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.
Let's personalize your content