Why Data Science Isn't an Exact Science
Information Week
JULY 27, 2020
Organizations adopt data science with the goal of getting answers to more types of questions, but those answers are not absolute.
Information Week
JULY 27, 2020
Organizations adopt data science with the goal of getting answers to more types of questions, but those answers are not absolute.

Information Week
JULY 31, 2020
Data science algorithms are never a one-size-fits-all solution. Do you know what makes sense for your business?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
JULY 29, 2020
Forrester’s view on the future of banking is here – examining the changes that we expect to play out over the next decade of retail banking. The drivers of the future are evolutions of the past – some playing out now, others that will be far more prominent by 2025 and table stakes by 2030. […].

Tech Republic Security
JULY 28, 2020
Read about the saga of Facebook's failures in ensuring privacy for user data, including how it relates to Cambridge Analytica, the GDPR, the Brexit campaign, and the 2016 US presidential election.

Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.
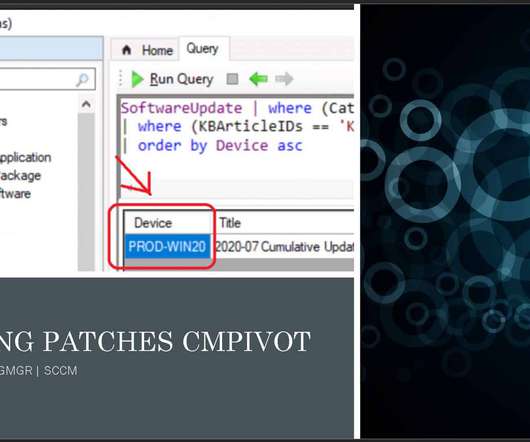
Anoop
JULY 28, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Let’s Find Missing Patches using ConfigMgr CMPivot Query. I have seen many questions in HTMDForum that we want the patch report using the SQL query. In this post, you will learn how to use the SCCM CMPivot query to find out missing patches. You can customize the CMPivot query as per your need and requirement.

Information Week
JULY 29, 2020
Here's how IT leaders can better manage the bias that becomes embedded in algorithms and datasets to help increase opportunities for minority tech professionals.
Information Technology Zone brings together the best content for IT professionals from the widest variety of industry thought leaders.

Tech Republic Security
JULY 29, 2020
While 56% of Americans want more control over personal data, more than 40% said they reuse passwords, use public Wi-Fi, or save a credit card to an online store, KPMG found.
Anoop
JULY 31, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Let’s learn how to troubleshoot out of band hotfix installation logs. You can find more details about the troubleshooting steps in this blog post. SCCM Troubleshooting Out of Band Hotfix Logs | ConfigMgr. NOTE! – More details available Dmpdownloader.log ( DMP Downloader Troubleshooting with State Messages).
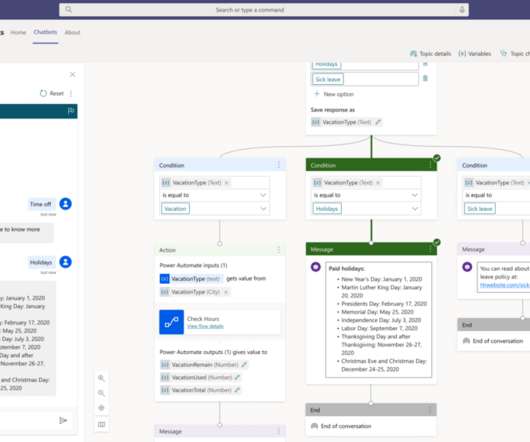
Tech Republic Cloud
JULY 31, 2020
Microsoft has provided more information on Dataflex, its new low-code platform for building apps and bots directly within Teams.

Forrester IT
JULY 28, 2020
A decade ago I completed the first ever assessment of Australia’s emerging “trusted” or private Infrastructure-as-a-Service (IaaS) market. I followed this up with a 2010 opinion-editorial calling for improved “cloud computing regulation” in Australia as a model for global oversight of a hugely important market segment.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Tech Republic Security
JULY 29, 2020
A recent investigation by NordPass and a white hat hacker discovered more than 9,000 unsecured databases online with more than 10 billion individual entries.
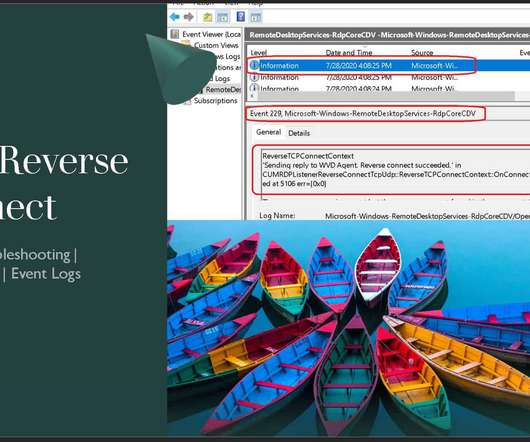
Anoop
JULY 30, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Let’s quickly go-through the WVD event logs using TCP Reverse Connect technologies. You can check this internal process of RDP connection through the secure channel from Windows 10 devices. I have a WVD Troubleshooting Options Tips Tricks – Windows Virtual Desktop in the previous post.

Tech Republic Cloud
JULY 31, 2020
Commentary: Diamanti started off as a way to make on-premises Kubernetes deployments sing. Now it's aiming to extend that to the cloud.

Forrester IT
JULY 31, 2020
Low-code platforms speed delivery of applications, but are they secure? The answer is more complicated than I expected when I started this research project with my colleagues, John Bratincevic and John R. Rymer. We’re still gathering information, but we’ve discovered that: Low-code security is not well understood. Even vendors with extensive security investments acknowledged that […].

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
Tech Republic Security
JULY 29, 2020
PQShield, a spin-out from the UK's Oxford University, is developing advanced cryptographic solutions for hardware, software and communications to protect businesses' data from the quantum threat.
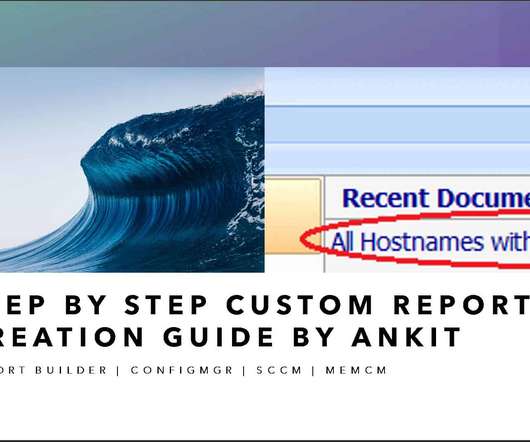
Anoop
JULY 29, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. If you are working as an SCCM Admin in your organization, you might have been asked to create custom reports (Create Custom Report Using Report Builder) according to customer requirements. As an admin, some create WQL queries and some prefer to work on SQL Queries and achieve their desired results.

Information Week
JULY 30, 2020
Looking to get a bigger bang from your budget? Think about optimizing some of your existing IT resources.

Forrester IT
JULY 28, 2020
The novel coronavirus shut down the US economy, freezing US consumer spending. This, however, is a temporary situation – consumers will resume spending when it is safe again for them to conduct regular commerce. So, the question customer experience (CX) professionals must ask their businesses is, “Are we positioned to recapture our clients once they […].

Advertisement
You’ve read the PMBOK® Guide several times, taken the certification exam for project managers, passed, and you are now a PMP®. So why do you keep making rookie mistakes? This whitepaper shows 20 of the most common mistakes that young or inexperienced project managers make, issues that can cost significant time and money. It's a good starting point for understanding how and why many PMs get themsleves into trouble, and provides guidance on the types of issues that PMs need to understand.

Tech Republic Security
JULY 31, 2020
New survey finds that cybersecurity professionals want more training to keep up with the threat landscape and learn new software platforms.

Anoop
JULY 30, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Let’s see how to create a custom SCCM Client Version Dashboard using a report builder and SQL query. Since the release of the Configuration Manager Current Branch, admins must analyze and keep their environment to the latest version of the client along with the server.

The Verge
JULY 30, 2020
Google is launching a new tool that allows businesses to identify themselves as Black-owned through the company’s Maps and Search listings. The new feature is part of the company’s pledge announced last month to support the Black community with “initiatives and product ideas that support long-term solutions.”. When searching for a business through Google.com or Google Maps, you’ll now be able to see a new badge to represent Black-owned businesses — it’s a black heart over an orange three-striped

Forrester IT
JULY 30, 2020
Marketers today must understand and use myriad technologies to support omnichannel ad strategies and deliver moments-based marketing. But the landscape of 7,000+ options is overwhelming and rapidly evolving, especially as new privacy regulations and tech giants like Apple and Google limit access to consumer data. We just published some research to help marketers keep up. […].

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Tech Republic Security
JULY 29, 2020
Dr. David Brumley, a professor at Carnegie Mellon University and CEO of ForAllSecure, explains what DevSecOps is and how companies can use it to improve security.
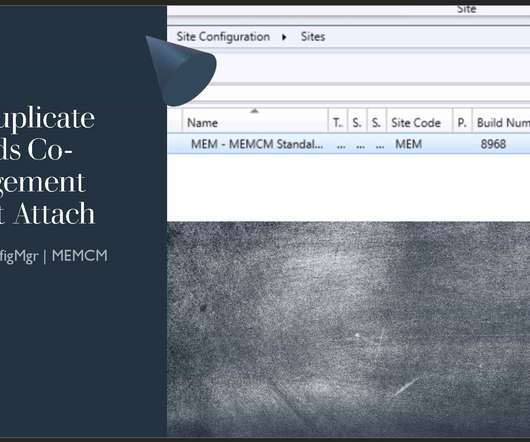
Anoop
JULY 27, 2020
Subscribe YouTube Channel [link]. and Facebook Page to get latest updates. [link]. Let’s understand how to Fix SCCM Duplicate Records when Co-Management & Tenant Attach is enabled. Microsoft recently released a new hotfix for ConfigMgr 2002. The KB 4575339 hotfix is released to fix the co-managed devices that are duplicated in the Microsoft Endpoint Manager admin center.

GeekWire
JULY 30, 2020
A United Launch Alliance Atlas 5 rocket sends NASA’s Mars Perseverance rover into space from its launch pad at Cape Canaveral Air Force Station in Florida. (ULA Photo). With the fiery flash of a rocket launch, NASA’s Perseverance rover headed out today for what’s expected to be a decade-long campaign to store up and bring back Martian samples that may hold evidence of alien life.

Gizmodo
JULY 28, 2020
In 2018, the world’s collective heart broke for Tahlequah, a Southern Resident killer whale in the Pacific Northwest that’s formal name is J35. The mama whale carried around her dead calf for more than two weeks. Now, Tahlequah is pregnant again. Read more.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Tech Republic Security
JULY 31, 2020
Professionals in the aerospace and defense industries should watch out; a wave of fake job offers containing malicious documents have been spotted in the wild by McAfee researchers.

The Verge
JULY 28, 2020
Fool an algorithm today: wear a mask. | Photo by Robin Utrecht/SOPA Images/LightRocket via Getty Images. Face masks are one of the best defenses against the spread of COVID-19, but their growing adoption is having a second, unintended effect: breaking facial recognition algorithms. Wearing face masks that adequately cover the mouth and nose causes the error rate of some of the most widely used facial recognition algorithms to spike to between 5 percent and 50 percent, a study by the US National

GeekWire
JULY 29, 2020
Zillow’s downtown Seattle offices in the Russell Investments Center, left, as seen from the nearby Pike Place Market. (GeekWire Photo / Kurt Schlosser). Zillow Group introduced a new policy on Wednesday allowing about 90% of its employees the option of working from home indefinitely, significantly extending a move the company made at the end of April in response to the coronavirus pandemic.

Gizmodo
JULY 26, 2020
Guillermo del Toro’s Frankenstein. The idea alone gives you chills. It’s been the director’s dream project for as long as he’s been asked the question, and the subject came up again at this weekend’s virtual San Diego Comic-Con. Del Toro explained a bit more about how he’d adapt the Mary Shelley book for the big… Read more.

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.
Let's personalize your content