The Anywhere Operating System
Forrester IT
FEBRUARY 22, 2022
“Do Operating Systems Matter Anymore?” It’s a common question in the end-user compute (EUC) industry, and it’s a reasonable one to ask.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Forrester IT
FEBRUARY 22, 2022
“Do Operating Systems Matter Anymore?” It’s a common question in the end-user compute (EUC) industry, and it’s a reasonable one to ask.

TM Forum
SEPTEMBER 12, 2022
The cloud-network operation system is an important part of the cloud-network convergence architecture, and it is also the key to unlocking the value of cloud-network convergence. China Telecom pays great attention to the technical research, and continuously optimizes cloud-network intelligent and agile operation capabilities.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
GeekWire
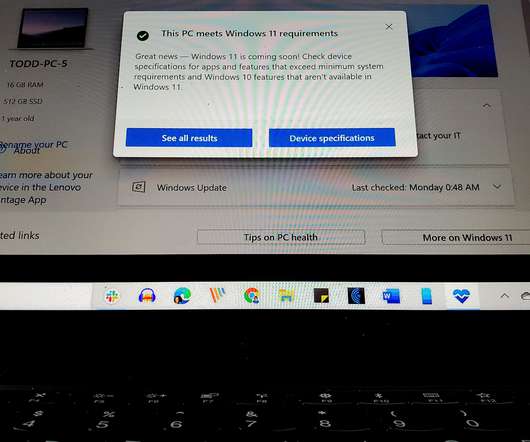
OCTOBER 4, 2021
Windows 11 is a free upgrade for computers and tablets running Windows 10, the operating system that Microsoft first released more than six years ago. Windows 11 is also a way for the company to boost the PC industry and bring additional attention to its own Surface devices. 5, the official launch day.

Forrester IT
MAY 20, 2017
Okay, I'll apologize right away to the IT ops teams that are already security-savvy. But I suspect there are still a few that leave security to the CISO's team. On Friday, May 12, 2017, evil forces launched a ransomware pandemic, like a defibrillator blasting security into the heart of IT operations. IT operations'.

CIO Business Intelligence
OCTOBER 4, 2023
This volatility can make it hard for IT workers to decide where to focus their career development efforts, but there are at least some areas of stability in the market: despite all other changes in pay premiums, workers with AI skills and security certifications continued to reap rich rewards.

CIO Business Intelligence
NOVEMBER 6, 2023
This makes it more critical than ever to adopt strong security measures to protect sensitive information and infrastructure. However, while cloud computing offers benefits like improved efficiency, scalability, and accessibility, it poses new security challenges.

Kitaboo
MARCH 30, 2024
Collaborating with digital textbook platforms like KITABOO empowers content creators to explore eBook security and ePUB DRM Solutions. In this comprehensive guide, we will learn more about the relevance of DRM systems and explore the best ePUB DRM Solutions ! Table of Contents: I. What is the Meaning of Digital Rights Management DRM?

CTOvision
JUNE 7, 2014
Security alarm systems have communicated with operations centers and police for a long time, but now allow monitoring and control from your smartphone. The goal is to better understand our world in order to improve resource management and predict dangers to safety and security in the physical world.

Kitaboo
MARCH 10, 2023
This gave rise to the need for a different kind of digital security to protect online content. Related Read: 6 Reasons Why You Need DRM Protected eBook There are several pros and cons of DRM for the publishing industry, here in this article we look at both sides of the coin.

Dataconomy
APRIL 4, 2024
According to the Data Breach Investigations Report, the human component of cyber security breaches comprises 82% of all confirmed data breaches. Viewed differently, this presents the ideal framework to implement sweeping security protocols designed to limit malfeasance, mitigate human error, and beef up workplace security.

Kitaboo
OCTOBER 7, 2021
In the last few years, the digital publishing industry has witnessed a tremendous spurt of growth. As a digital publisher, if you too have been facing a similar problem, here is a list of some major author platforms that you can employ to publish your content securely. An Industry Report – . Download Now!

CIO Business Intelligence
AUGUST 25, 2022
As organizations shape the contours of a secure edge-to-cloud strategy, it’s important to align with partners that prioritize both cybersecurity and risk management, with clear boundaries of shared responsibility. The security-shared-responsibility model provides a clear definition of the roles and responsibilities for security.”.

SecureWorld News
APRIL 9, 2023
This forces IT and information security specialists to constantly enhance protection to effectively counter information security incidents related to malware distribution through rogue websites, links, and email attachments. Traffic goes through filtering and security policies to ensure the user is only exposed to safe information.

CTOvision
NOVEMBER 22, 2016
Nature is now providing engineers with the missing link that can help with the most vexing challenge of our age: enabling both security and functionality in our interconnected IT systems. Cyberattacks are increasing across multiple industries and every level of government. Next generation cybersecurity is needed right now.

CTOvision
JUNE 3, 2014
They have a great portfolio of technologies needed by enterprises today and are helping make mobile workforces more secure, agile and productive. I believe this acquisition by Good Technologies will result in a very significant enhancement in the ability of enterprises to secure their mobile users. – bg. From: [link].

CIO Business Intelligence
JANUARY 20, 2023
By Anand Oswal, Senior Vice President and GM at cyber security leader Palo Alto Networks Connected medical devices, also known as the Internet of Medical Things or IoMT, are revolutionizing healthcare, not only from an operational standpoint but related to patient care. Many connected devices ship with inherent vulnerabilities.

Trends in the Living Networks
MAY 5, 2011
The final session was on Where Mobile is Going , which looked at the mobile industry landscape, as well as the implications of emerging technologies such as 4G and LTE, next generation augmented reality, NFC and mobile payments, new interfaces such as video glasses and pico projectors, mobile sensors, and far more. Impact of security issues.

CTOvision
FEBRUARY 5, 2014
Securing these devices is nearly impossible because they are not corporate controlled. This makes it difficult to enforce regulation and compliance in industries such as health care and finance where failure can cause lawsuits, fines, and other penalties. XP Will Cause Significant Security Issues.

SecureWorld News
MAY 7, 2024
According to a new joint cybersecurity alert , the hacktivists have been observed gaining remote access to small-scale industrial control systems used in water/wastewater, dams, energy, and food and agriculture by exploiting internet-exposed human-machine interfaces (HMIs) and using default or weak passwords.

Network World
APRIL 7, 2017
Department of Homeland Security (DHS) received reports of 59 cyber incidents at energy facilities in 2016. Security specialists believe this number is quite conservative, considering that energy companies aren’t required to report cyberattacks to DHS. This column is available in a weekly newsletter called IT Best Practices.

Kitaboo
NOVEMBER 9, 2020
This gave rise to the need for a different kind of digital security to protect online content. There are several pros and cons of DRM for the publishing industry, here in this article we look at both sides of the coin. However, platforms like KITABOO can give readers access to content on multiple devices across operating systems.

Dataconomy
MARCH 25, 2024
China is bolstering its semiconductor industry to lessen its dependence on foreign tech. Authorities above the township level are mandated to acquire processors and operating systems deemed “safe and reliable” as per the Financial Times. China has enacted new rules mandating the removal of U.S. and China.
The Verge
NOVEMBER 17, 2020
Microsoft is creating a new security chip that’s designed to protect future Windows PCs. Microsoft Pluton is a security processor that is built directly into future CPUs and will replace the existing Trusted Platform Module (TPM), a chip that’s currently used to secure hardware and cryptographic keys.

CIO Business Intelligence
MARCH 8, 2023
As organizations shape the contours of a secure edge-to-cloud strategy, it’s important to align with partners that prioritize both cybersecurity and risk management, with clear boundaries of shared responsibility. The security-shared-responsibility model provides a clear definition of the roles and responsibilities for security.”

TM Forum
OCTOBER 27, 2022
Settlement rules change often, and associated documents are cumbersome – while reconciliations are often manual and offline, using non-transparent, cleartext datasets, meaning inherent problems around security and trust. And how can a suitably efficient operation system be achieved so that all parties can enjoy cost reduction?

SecureWorld News
MARCH 23, 2021
The increased connectivity brought on by the Industrial Internet of Things (IIoT) allows for more real-time monitoring and adjustment of power, but with those benefits also comes greater risk. The recent SolarWinds incident has highlighted the importance of securing critical infrastructure in the U.S., including the electricity grid.

The Verge
AUGUST 11, 2021
Apple has settled its copyright lawsuit against Corellium, a company that sells virtual iPhone environments for security testing. The terms of the settlement are confidential, but Corellium confirmed to The Washington Post that it would continue to offer virtual iOS systems. Illustration by Alex Castro / The Verge.

CIO Business Intelligence
OCTOBER 20, 2023
Whether you’re just starting out and building your resume or you’ve been in the industry for 20 years, there’s a certification that can help boost your salary and your career.

Dataconomy
MAY 8, 2023
However, much like the vast expanse of space, the cloud can be a dangerous place without proper security measures in place. To navigate this cosmic challenge, the shared responsibility model has emerged as a guiding light in the world of cloud computing security. Customer responsibilities: Securing their own applications and data.

SecureWorld News
AUGUST 10, 2020
Microsoft and other industry professionals strongly recommend upgrading computer systems to an actively supported operating system.". When an operating system reaches its End of Life, it becomes a prime target for hackers. The healthcare industry is already under major stress amid COVID-19.

CIO Business Intelligence
AUGUST 25, 2022
In manufacturing and engineering facilities, PLCs (programmable logic controllers) have been attenuating and monitoring industrial devices since the invention of the microchip. This raises new questions about managing and operating these devices in a consistent, reliable, and secure manner. Operating Systems for the edge.

Dataconomy
JUNE 14, 2023
This rampant practice poses significant challenges to the creative industries, encompassing film, music, publishing, software development, and gaming. Its repercussions are far-reaching, casting a shadow of concern upon various creative industries, spanning from the captivating realms of film, television, publishing, music, and gaming.

CTOvision
DECEMBER 16, 2013
The acquisition and this new round of funding support Invincea’s rapid growth across the globe, expansion into the small business sector, and further solidifies its position as the market leader in this game changing cyber-security segment. FAIRFAX, VA–(Marketwired – Dec 16, 2013) – Invincea, Inc.,

Forrester IT
MAY 15, 2017
For years, many of us in the cybersecurity industry have been jumping up and down on desks and trying to get the world (writ large) to pay attention to managing and patching outdated systems and operating systems that have been running legacy software, to no avail. cyber security. Read more Categories: #big data.

CIO Business Intelligence
MAY 26, 2023
It’s a solid choice as an entry-level certification that is well-regarded in the industry and will verify that you have the skills to troubleshoot and resolve problems around networking, operating systems, mobile devices, and security. To earn the certification, you’ll need to pass two exams.

ForAllSecure
MAY 16, 2023
In a perfect world, your software testing strategy would surface all of the security risks that exist inside your environment, and nothing more. Sometimes, the security issues that software testing tools flag turn out to be false positives. What Are False Positives in Software Security Testing?

SecureWorld News
JUNE 12, 2023
Cybersecurity professionals are increasingly turning to online courses to earn their credentials, helping them stand out from the crowd and keep pace with an ever-changing industry. Some courses are tailored to a specific discipline, while others may be broader, covering areas such as network security , ethical hacking, and more.

TM Forum
NOVEMBER 7, 2022
I am an Enterprise Architect at CGI, leading transformation programs to deliver core business and operational systems for Communication Service Providers. At CGI, we help our customers in their digital transformation journey by modernizing legacy systems with purpose-built and future-ready solutions aligned to industry standards.

CIO Business Intelligence
JANUARY 19, 2023
To become a software-powered organisation, companies must first identify and address the concerns of its developers in areas such as developer experience, developer velocity and software security. For example, close to 60% of respondents are using OSS for Database and 53% for Operating Systems.

SecureWorld News
SEPTEMBER 8, 2021
For the healthcare industry, this became more complicated amidst the pandemic. He also urges healthcare organizations to take the following steps to protect patient data: "Keep all operating systems and software housing health data current with the latest security patches;".

Dataconomy
SEPTEMBER 27, 2023
The Microsoft Certified Solutions Associate and Microsoft Certified Solutions Expert certifications cover a wide range of topics related to Microsoft’s technology suite, including Windows operating systems, Azure cloud computing, Office productivity software, Visual Studio programming tools, and SQL Server databases.

GeekWire
NOVEMBER 26, 2023
” It’s called the Amazon WorkSpaces Thin Client, using the industry lingo for a basic type of hardware that relies on cloud-based storage and processing rather than a beefy CPU and hard drive on a traditional computer. Other potential use cases include students in computer labs, and work-from-home employees.

TM Forum
NOVEMBER 7, 2022
I am an Enterprise Architect at CGI, leading transformation programs to deliver core business and operational systems for Communication Service Providers. At CGI, we help our customers in their digital transformation journey by modernizing legacy systems with purpose-built and future-ready solutions aligned to industry standards.

Network World
JULY 14, 2017
The Internet of Things, at its simplest level, is smart devices - from refrigerators that warn you when you’re out of milk to industrial sensors – that are connected to the Internet so they can share data, but IoT is far from a simple challenge for IT departments.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content