Technology Short Take 176
Scott Lowe
MARCH 15, 2024
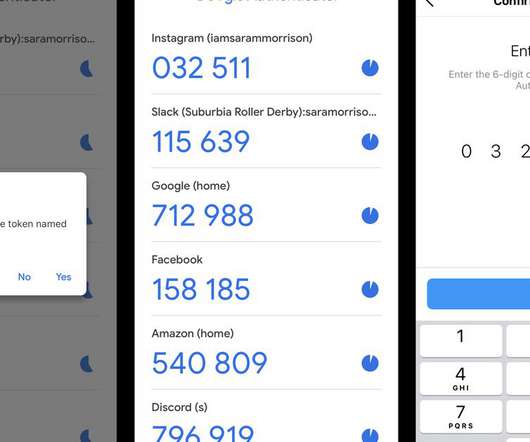
And here’s another example of malware that is targeting Linux (along with Windows). This would be why I hate it when companies force me to use SMS for two-factor authentication—at least let me use a one-time passcode or something. Rory McCune explains Kubernetes authentication. Falco has graduated within the CNCF.















































Let's personalize your content