Zoom’s mobile and desktop apps now support two-factor authentication
The Verge
SEPTEMBER 11, 2020
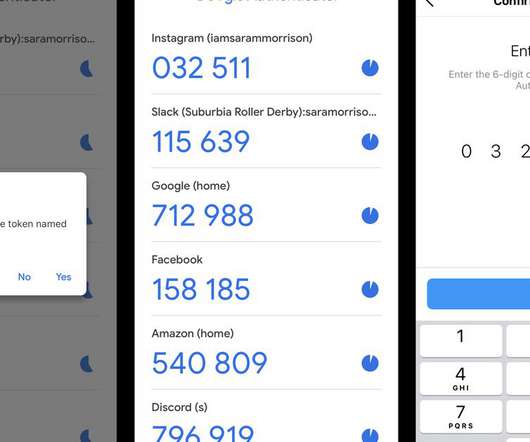
Zoom is adding support for two-factor authentication (2FA) to its desktop and mobile applications, giving users the option of adding an extra layer of security to their account beyond a standard password, the company has confirmed to The Verge. Illustration by Alex Castro / The Verge. 2FA codes over SMS are also now supported.













































Let's personalize your content