Information Stealing Malware on the Rise, Uptycs Study Shows
SecureWorld News
JULY 27, 2023
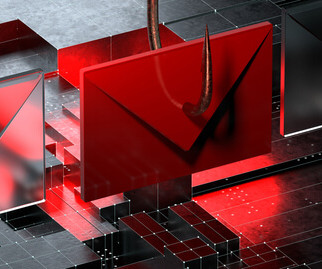
A new study from Uptycs has uncovered an increase in the distribution of information stealing malware. Newly discovered stealer families include modules that specifically steal logs from MFA applications, like the Rhadamanthys malware. Examining the dark web reveals that infostealer malware has become increasingly widespread.

















































Let's personalize your content