How to Prevent Phishing Attacks with Multi-Factor Authentication
Tech Republic Security
JANUARY 25, 2024
Learn how to protect yourself and your sensitive information from phishing attacks by implementing multi-factor authentication.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JANUARY 25, 2024
Learn how to protect yourself and your sensitive information from phishing attacks by implementing multi-factor authentication.

Tech Republic Security
JUNE 11, 2020
A password alone will not protect sensitive information from hackers--two-factor authentication is also necessary. Here's what security pros and users need to know about two-factor authentication.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CTOvision
NOVEMBER 4, 2014
With the movement of our personal and business critical data to the ‘cloud’, and directed attacks on that data, many of us make use of stronger security through use two-factor authentication. According to Google, security keys provide better protection against phishing and you don’t need connections or batteries.

Tech Republic Security
MARCH 17, 2022
The first line of defense against ransomware lies with email authentication. Learn more information about how to take a proactive approach to cyber attacks. The post Email authentication helps governments and private companies battle ransomware appeared first on TechRepublic.

Advertisement
Think your customers will pay more for data visualizations in your application? Five years ago they may have. But today, dashboards and visualizations have become table stakes. Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Brought to you by Logi Analytics.

SecureWorld News
FEBRUARY 15, 2024
A sophisticated form of mobile malware dubbed "GoldPickaxe" has been uncovered, which collects facial recognition data to produce deepfake videos, enabling hackers to bypass biometric authentication protections on banking apps. Experts warn that biometric authentication alone is not foolproof.

CIO Business Intelligence
NOVEMBER 6, 2023
This makes it more critical than ever to adopt strong security measures to protect sensitive information and infrastructure. However, while cloud computing offers benefits like improved efficiency, scalability, and accessibility, it poses new security challenges.

CTOvision
FEBRUARY 20, 2020
Facebook recently pledged to improve its security following a lawsuit that resulted from a 2018 data breach. The breach, which was left open for more than 20 months, resulted in the theft of 30 million authentication tokens and almost as much personally identifiable information.

CIO Business Intelligence
OCTOBER 25, 2023
On October 20, 2023, Okta Security identified adversarial activity that used a stolen credential to gain access to the company’s support case management system. The recent compromise of a leading IdP provider isn’t the first time adversaries gained access to critical customer information, and it won’t be the last.

CIO Business Intelligence
OCTOBER 26, 2022
Digitalization is a double-edged sword for banks, especially when it comes to security. As interactions and transactions become more interconnected, even the simplest processes like opening a new account or making a balance transfer become riddled with security concerns. Avaya’s research report reveals three critical ways to do so.

Galido
FEBRUARY 25, 2020
Information Technology Blog - - The Small Business Guide to Information Security - Information Technology Blog. Information security is a major issue in the business world, and security breaches cost businesses millions of dollars per year. But they can be particularly disastrous to small businesses.

SecureWorld News
MARCH 10, 2021
GitHub announced a security update due to a bug causing issues with the authentication of sessions. On March 2, GitHub received an external report of anomalous behavior for their authenticated GitHub.com user session. This would give them the valid and authenticated session cookie for another user.

The Accidental Successful CIO
JANUARY 23, 2019
Everybody needs two factor authentication, but just exactly what is it? As everyone in the CIO position knows, keeping the company’s systems and applications secure is a top priority and has a lot to do with the importance of information technology. Two Factor Authentication. Image Credit: Dave Crosby.

CIO Business Intelligence
JUNE 27, 2022
One of the best ways to ensure security? Multi-factor authentication, or MFA. Multi-factor authentication requires users to provide two or more pieces of evidence in order to gain access to a network, application, or system, and can dramatically decrease the likelihood of infiltration. IT Leadership, Security

Gizmodo
DECEMBER 28, 2021
Two-factor authentication, or 2FA, has been sold to web users as one of the most important and trustworthy tools for securing your digital life. You probably know how it works : By supplying an account with not just your password but also a secondary piece of information (typically an automated code texted to your… Read more.

SecureWorld News
SEPTEMBER 5, 2023
In a recent revelation, security researcher Jeremiah Fowler uncovered a significant data leak affecting one of the United States' largest health insurance companies, Cigna Health. The database, astonishingly lacking password protection, contained a wealth of information pertaining to Cigna Health and its vast network of healthcare providers.

Kitaboo
APRIL 25, 2024
Accessing, consuming, transferring information, and digitizing books has become increasingly easy in the modern age. Digital Rights Management (DRM) protection is a primary mechanism to protect eBooks from piracy while ensuring readers can access content securely. Let’s find out more. Table of Contents I. What is DRM Protection?

CTOvision
AUGUST 15, 2014
Stage 2 requires expanded use of patient portals, as well as implementation of secure messaging, allowing patients to exchange information with physicians regarding their health care. Secure Messaging Requires Authentication and Secure Networks. Patient Portal and Messaging Authentication.

Forrester IT
OCTOBER 1, 2020
Biometric authentication is a powerful technology with many compelling use cases but is not without controversy and distinct risks. What are users’ privacy rights in how biometric information is processed and stored? What security shortcomings are associated with […]. How are biometrics regulated around the world?

Dataconomy
APRIL 2, 2024
Meanwhile, strong security builds customer trust, which is essential for lasting relationships and business stability. From e-commerce and online banking to subscription services and digital marketplaces, the demand for secure online payments has never been higher. Let’s examine these security features in more detail.

Association of Information Technology Professional
SEPTEMBER 24, 2021
2FA is widely used to improve an organization’s security. Learn why IT pros are expected to know how to explain and integrate it into IT environments.

SecureWorld News
JANUARY 10, 2024
Securities and Exchange Commission's (SEC) account on X (formerly Twitter) was briefly compromised on Tuesday, January 9, sending shockwaves through the cryptocurrency market and raising serious questions about the agency's cybersecurity practices. Additionally, promoting transparency in response to security incidents is crucial.

CIO Business Intelligence
SEPTEMBER 7, 2023
Slowing the progression of AI may be impossible, but approaching AI in a thoughtful, intentional, and security-focused manner is imperative for fintech companies to nullify potential threats and maintain customer trust while still taking advantage of its power. Misinformation and manipulation of data.

SecureWorld News
FEBRUARY 17, 2024
New security solutions are now aiding healthcare organizations' IT teams in promptly resolving issues, even with devices from various manufacturers. Let's examine common security challenges in connected healthcare equipment and discuss some effective protection strategies and recommendations.

Computer Weekly
JUNE 28, 2016
How can organisations move to biometric authentication of users without running the risk of exposing sensitive biometric information?
Dataconomy
JANUARY 10, 2024
Whether it’s records or customer information, data holds value. However, given the increasing reliance on technology and the growing number of cyber threats, ensuring data security has become crucial. In this post, we will explore the role of managing data security in the landscape.
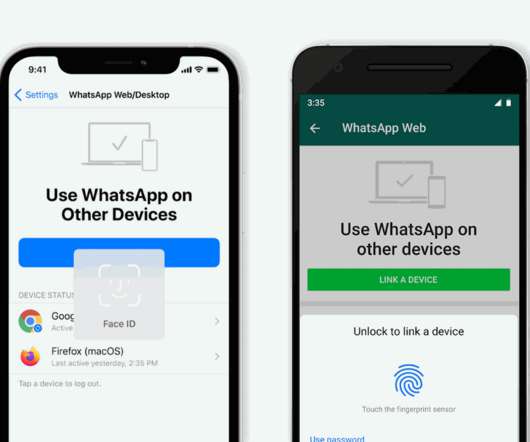
The Verge
JANUARY 28, 2021
Linking your WhatsApp account to your computer’s web browser or desktop app is getting a little more secure. Soon, if you’ve got biometric authentication enabled on your phone, you’ll have to unlock the app before you can link your account.

TechSpot
OCTOBER 1, 2021
It features two-factor authentication and now includes a "Masked Email" option. Available for the vast majority of operating systems, 1Password stores all your passwords and can be also used as a digital wallet. Though it is not free, you can try it for 14 days here.

CTOvision
SEPTEMBER 12, 2014
This gathering, facilitated by the Transglobal Secure Collaboration Participation (TSCP) pulls together leaders in real secure information exchange, including information exchange across and between enterprises. Join the Leaders in Secure Collaboration. Organized by the Industry Leader in Secure Collaboration.

SecureWorld News
FEBRUARY 23, 2023
In a breach that's making headlines, hackers managed to steal data from the company, including sensitive employee information and upcoming game content. vx-underground also reported that a hacker managed to break into an Activision Slack channel, post offensive messages, and steal information related to upcoming "Call of Duty" releases.
Kitaboo
DECEMBER 18, 2023
Literacy is often regarded as a puzzle piece that is difficult to fit into the evolving jigsaws of information dissemination. As the channels of information spread grew multifold and information access was more digitalized, ‘ digital literacy ‘ became the norm. Conclusion What is Digital Literacy?

The Verge
OCTOBER 5, 2021
In May, Google announced plans to enable two-factor authentication (or two-step verification as it’s referring to the setup) by default to enable more security for many accounts. In 2018, Google said that only 10 percent of its active accounts were using two-factor authentication. Illustration by Alex Castro / The Verge.

Tech Republic Security
SEPTEMBER 21, 2022
In last week’s security breach against Uber, the attackers downloaded internal messages from Slack as well as information from a tool used to manage invoices. The post Uber exposes Lapsus$ extortion group for security breach appeared first on TechRepublic.

Dataconomy
JANUARY 24, 2024
This has led to a necessity for additional security measures to be implemented in online systems to protect businesses online. Having a rigorous SAP security strategy in place is important to control access to a business’s sensitive data and monitor the SAP environment for unusual activity and potential threats.

ForAllSecure
OCTOBER 6, 2022
For most APIs, the next step is setting up authentication. After all, without successfully authenticating, Mayhem for API can only test for very superficial problems! Giving the fuzzer a way to authenticate to the target API will enable it to exercise more endpoints and maximize coverage. Basic Authentication.

Network World
JUNE 30, 2023
To reduce the risk of service problems, Cisco is making it harder for organizations to use weak cryptographic algorithms when setting up authentication for OSPF packets on certain Catalyst Edge Platforms and Integrated Services Routers (ISR). Newer versions of Cisco’s IOS XE software (Release 17.11.1

CIO Business Intelligence
MAY 2, 2022
Password-based authentication is likely the most widely used method of authenticating users to online services. Password-based authentication is used because it is easy to understand and implement. However, this comes at the cost of weak security and a poor user experience. Password-based authentication isn’t working.

CIO Business Intelligence
JANUARY 9, 2024
Achieving and sustaining compliance with the Payment Card Industry Data Security Standard (PCI DSS) is a daunting challenge for hotels because they handle many complex payment business cases. See the PCI Security Standards Council (SSC) Requirements and Testing Procedures , Version 4.0 Four recommended steps in the PCI DSS v4.0

Dataconomy
NOVEMBER 21, 2023
The government of Canada has revealed the big “Canada data breach” that consists of information about government personnel, members of the Royal Canadian Mounted Police (RCMP), Canadian Armed Forces personnel, and more. Smelling something fishy in your accounts?

Kitaboo
MARCH 30, 2024
Leading digital textbook platforms like KITABOO, which incorporate DRM systems, play a pivotal role in data security. Data security has become the need of the hour, considering the growth in piracy, illicit distribution of content, and misuse of intellectual property. To get started with DRM, connect with us now !

HID Global
JANUARY 31, 2023
RFID is a flexible secure and efficient wireless system used to exchange information effortlessly between devices and layers of protection and usability.

SecureWorld News
JULY 27, 2023
A new study from Uptycs has uncovered an increase in the distribution of information stealing malware. The 17-page report has a wealth of information, including the impact of stealers, the lifecycle of a stealer, the workflow of a stealer, and statistics around the stealers trending in 2023.

SecureWorld News
APRIL 2, 2024
However, mounting evidence from cybersecurity researchers pointed to the data being authentic AT&T customer records. The compromised data includes names, addresses, phone numbers, and for many, highly sensitive information like Social Security numbers and dates of birth. "AT&T million former account holders."

CIO Business Intelligence
DECEMBER 19, 2023
When making decisions about network access, businesses need to be aware of and assess the security implications associated with network technology to help keep their digital assets protected. Cyber hygiene best practices include device security , cyber security education , and secure networking strategies.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content