Authentic Artists creates AI virtual artists for gaming and streaming
Venture Beast
APRIL 7, 2021
Authentic Artists is launching a new AI-powered platform to create virtual artists for gaming and streaming apps. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
APRIL 7, 2021
Authentic Artists is launching a new AI-powered platform to create virtual artists for gaming and streaming apps. Read More.

Tech Republic Security
SEPTEMBER 14, 2022
Virtually every business today is a technology business, relying on digital services in some way to serve and support their customers. The post Goodbye Friction, Hello Flow: 6 Ways to Build Trust with Strong Customer Authentication appeared first on TechRepublic. The pandemic has driven services online faster than.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Venture Beast
JANUARY 26, 2022
Just as identity and authentication is pivotal to today's world, the metaverse will also require people to prove who they are. Read More.

Kitaboo
FEBRUARY 16, 2021
The emergence of digital content and its prevalence during the pandemic has given rise to virtual textbooks. This blog post explains how virtual textbooks are different and even better than printed textbooks in many ways. How Can Publishers Benefit From Virtual Textbooks? Virtual Textbooks Are Easier to Update.

GeekWire
JANUARY 1, 2021
Real, authentic fireworks shows are pretty amazing. But the virtual version isn’t too shabby, either. ” Watching the virtual show in the comfort of your own home isn’t a bad option. Instead, like many groups this year, they pivoted. — Jess Zimbabwe (@jzimbabwe) January 1, 2021.

The Verge
DECEMBER 13, 2021
RTFKT claims that in February, a collaboration with teenage artist FEWOCiOUS to sell real sneakers paired with virtual ones managed to sell some 600 pairs/NFTs in just six minutes , netting over $3.1 million at the time.
The Verge
DECEMBER 29, 2020
Apple has lost an early challenge in its lawsuit against Corellium, a security firm that offers a virtualized version of iOS for security testing. Apple has alleged that Corellium circumvented its authentication server and secure boot chain, among other measures, violating the DMCA’s ban on circumventing copy protection measures.
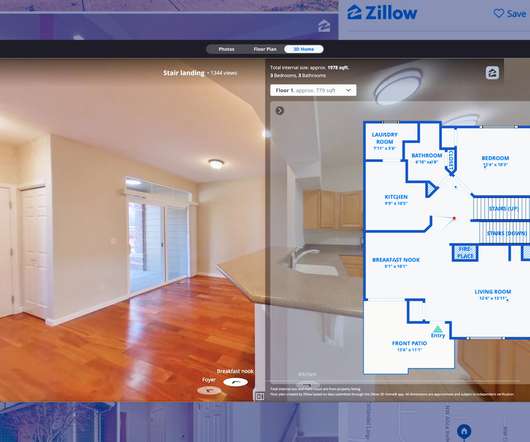
GeekWire
FEBRUARY 17, 2021
Zillow Group on Wednesday rolled out a new feature for its virtual tour experience that uses machine learning to pull together various media content with an interactive floor plan. “It allows the shopper to have a deeper, more authentic sense of home,” said Josh Weisberg, VP of Zillow’s Rich Media Experience team. .

Venture Beast
JUNE 30, 2021
Drop Fake has raised $9 million in seed round funding for a game studio that focuses on authentic fan experiences. Read More.
Network World
APRIL 4, 2023
FortiOS is the operating system for the FortiGate family hardware and virtual components, and it implements Fortinet Security Fabric and includes firewalling, access control, Zero Trust, and authentication in addition to managing SD-WAN, switching, and wireless services. FortiOS version 7.4
Dataconomy
SEPTEMBER 14, 2023
Document management has been transformed by virtual data room due diligence. To store, organize, and securely communicate data with business partners during an M&A transaction is the job of virtual data room management software. These include modern encryption techniques and a multi-level authentication process.

Network World
APRIL 7, 2022
Virtualization and cloud vendor VMware this week disclosed eight vulnerabilities in five of its products , and urged users of Workspace ONE Access and all its products that include VMware Identity Manager components to patch immediately. To read this article in full, please click here

GeekWire
MARCH 14, 2024
. “It is a two-sided marketplace platform, where authentic creators (authors or others with their own proprietary content) can build a conversational AI that is grounded in the content they bring,” Sirosh told GeekWire via email.

Scott Lowe
MARCH 15, 2024
The vulnerability affects virtually all Linux distributions and allows attackers to bypass the secure boot protections and insert a low-level bootkit. This would be why I hate it when companies force me to use SMS for two-factor authentication—at least let me use a one-time passcode or something.

Network World
AUGUST 21, 2016
Security researchers continue to find ways around biometric-based security features, including a new attack which can defeat face authentication systems. You might be careful about posting photos of yourself online, either refraining from it or setting the images to private, but your “friends” might post pictures of you online.

Network World
APRIL 4, 2022
FortiOS is the vendor’s operating system for the FortiGate family of hardware and virtual components. FortiOS implements Fortinet Security Fabric and includes network security such as firewalling, access control, and authentication in addition to SD-WAN, switching, and wireless services. How to choose an edge gateway.
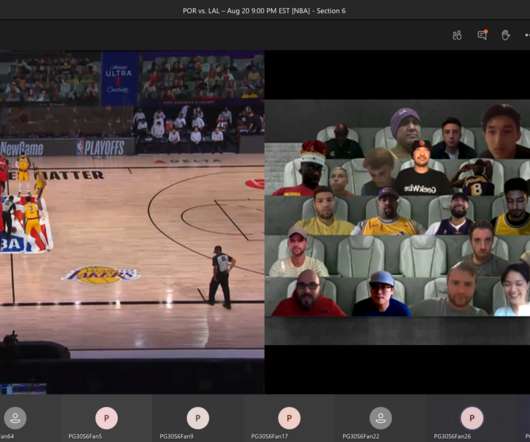
GeekWire
AUGUST 21, 2020
This is the spectator view for fans watching NBA games “courtside” in Microsoft Teams: the live stream on one side, and your virtual cheering section on the other. My big takeaway: Microsoft and the NBA are on to something with their new tech-fueled virtual fan experience. Look out for me in the virtual stands!!!

GeekWire
DECEMBER 18, 2020
Seattle-based FFA just wrapped up a virtual version of its eight-week Ready Set Raise program, which requires each company to have a female or non-binary CEO. The pitch: “Fix Fake delivers risk-scoring software to automate authentication and find fakes for e-commerce marketplaces. ” Company: Health In Her HUE.

CIO Business Intelligence
DECEMBER 17, 2023
Customers can start a chat session, speak with a virtual bot , or even send a text message and engage in a natural and conversational way with immediate, personalized assistance 24/7– always with the option to escalate to a human during set business hours. Clear communication means fewer distractions and requests to repeat information.

Phil Windley
AUGUST 28, 2023
My new book Learning Digital Identity from O'Reilly Media covers many of the topics in this post such as multi-factor authentication, authorization and access control, and identity policy development in depth. User Authentication: Multi-Factor Authentication (MFA): Requiring users to provide multiple forms of verification (e.g.,

CTOvision
OCTOBER 17, 2019
Read George Platsis take a look at whether the authentication systems will run into the privacy wall on Security Intelligence : Identity authentication is absolutely necessary to conducting our affairs today. Without it, we would lose virtually all confidence to conduct business or create and foster relationships.

TechSpot
MARCH 10, 2021
As the Pixels can communicate their rolls to a phone or tablet, they can be used with online tabletop platforms such as Roll20 and Foundry, enabling a more authentic experience when playing virtual RPG campaigns.

Future of CIO
JANUARY 12, 2016
An organization with an authentic culture can inspire openness, innovation and motivational. So what are the fundamental elements to build an authentic culture in order to run a high-valuable and high-mature digital organization? Culture is the collective mindset, attitudes, and behaviors. Also, communication is a two-way street.

Kitaboo
APRIL 25, 2024
Thus, DRM can be understood as a virtual lock enabling access only to those who have acquired it legally. The authorization can be conferred through various means, such as license keys, digital certificates, or online authentication. can monitor who can access the content and from where.

Vox
NOVEMBER 12, 2023
Access to just about everything I wasn’t already logged into on my computer was dependent on access to my phone, with my mobile-device-only password manager and multifactor authentication apps and text messages. Would it even be possible to log in, since my passwords and authentication tools were only on the phone? “I

Network World
OCTOBER 22, 2019
Cisco this week said it issued a software update to address a vulnerability in its Cisco REST API virtual service container for Cisco IOS XE software that scored a critical 10 out of 10 on the Common Vulnerability Scoring System (CVSS) system. To read this article in full, please click here

Network World
JUNE 18, 2018
With Windows Server 2019, Microsoft is adding resiliency and redundancy enhancements to the Shielded Virtual Machines security controls it introduced with Windows Server 2016. Under Windows Server 2016, key authentication was based on trusted platform module (TPM) cryptoprocessors and Microsoft Active Directory authentication.

CIO Business Intelligence
MAY 31, 2022
The metaverse will require a digital foundation that enables trust and authenticity. This comes with a learning curve as, for instance, people may not yet be familiar with virtual reality (VR) and augmented reality (AR) platforms and terms and protocols related to Web 3—essentially the next iteration of the internet. Building trust.

Kitaboo
DECEMBER 27, 2023
10 Ways in Which Artificial Intelligence (AI) Can Change the Future of Content Automates Repetitive Tasks SEO Optimization Machine Translation Emotion Analysis Natural Language Processing (NLP) Fraud Detection Content Personalization Automated Transcription Services Creative Assistance Voice Recognition Through Chatbots and Virtual Assistants III.

Kitaboo
DECEMBER 20, 2023
The arrival of the virtual school is seeing K12 students engaging with teachers and peers in virtual classrooms. Ensuring Data Security For Digital Education Products Focus On Digital Rights Management Leverage User Authentication Watermark Documents Register eTextbooks III. Table of contents: I.

CIO Business Intelligence
JUNE 23, 2022
Virtual Private Networks (VPNs) have long been the go-to method for providing remote users secure access to the corporate network. In 2021, Gartner saw a 127% increase in interest about ZTNA, compared to the prior year – and most of the use cases centered on ZTNA as a replacement for Virtual Private Networks (VPNs).

CIO Business Intelligence
AUGUST 14, 2023
Cherokee Nation had run digital campaigns in the past, but the systems in place could not authenticate citizenship, leaving a significant amount of manual labor behind each interaction. COVID-19 expedited the need for a digital platform to handle authentication and meet the spike in demand for assistance in the wake of a global pandemic.

GeekWire
JANUARY 11, 2023
Unlike those who work in the company’s stores, Starbucks corporate employees have had the “privilege” to work virtually, Schultz said. We must have authentic and deep human connection everywhere we work,” he wrote. Howard Schultz in 2017. GeekWire File Photo / Kevin Lisota). “We need to rebuild that.

Kitaboo
NOVEMBER 30, 2023
They can also rest assured that they have access to the latest, most authentic content, that hasn’t been tampered with. How DRM Protection Works DRM protection involves a combination of encryption, licensing, and authentication mechanisms.

The Verge
MARCH 8, 2021
Facebook’s future virtual reality headsets should capture users’ facial expressions for more realistic digital avatars, says CEO Mark Zuckerberg. In a podcast interview for The Information , Zuckerberg expounded on the next decade in virtual and augmented reality, including future Oculus VR devices.

SecureWorld News
JUNE 23, 2020
SecureWorld Panel: Identity, Authentication, and the Remote Workforce. Three SecureWorld panel speakers for "Identity, Authentication, and the Remote Workforce" have answers. He said: "We power a lot of the authentication and authorization under some of the biggest brands in the world. Licata] "I always go back to process.

The Verge
OCTOBER 22, 2020
the new accounts will offer two-factor authentication and safety features previously available in the ‘Bedrock Edition’ of the game. Players have requested two-factor authentication for as long as the game has offered a place to buy and sell content — that’s three years, if you’re counting.

CTOvision
JANUARY 4, 2017
The foundational security control to stop credential theft is 2 factor authentication. Protect Data Encryption and Virtual Desktops. Many IT managers assume that by encrypting data or putting it behind a virtual desktop they are safe they are safe from theft. Partition Supply Chain Resources.

SecureWorld News
DECEMBER 8, 2021
"Use of novel TTPs to bypass security restrictions within environments including, but not limited to the extraction of virtual machines to determine internal routing configurations.". Abuse of multi-factor authentication leveraging 'push' notifications on smartphones.". Use of a new bespoke downloader we call CEELOADER.".

SecureWorld News
JULY 13, 2022
Yes, while you are out on vacation enjoying all the good things that come with summer, cybercriminals are still hunkered down in their virtual caves creating new phishing schemes to make everyone's lives more difficult. Microsoft says the AiTM phishing campaign has attempted to target more than 10,000 organizations since September 2021.
The Verge
JUNE 24, 2021
You’ll need to sign in using an Apple Music or Spotify Account, and then it’s a simple case of using the virtual click wheel to select and listen to a selection of your most listened-to artists. It’s at its worst when loading up the virtual iPod’s built-in Brick Breaker game clone (which, sidenote, also rips). Perfection.

Network World
MAY 23, 2017
When it comes to security and the iris recognition technology used in its flagship Galaxy S8 smartphone, Samsung touted , “The patterns in your irises are unique to you and are virtually impossible to replicate, meaning iris authentication is one of the safest ways to keep your phone locked and the contents private.”

CIO Business Intelligence
JULY 10, 2023
Traditional identity verification methods like knowledge-based authentication (e.g. The bot then provides a link to enter the university’s self-composed Metaverse (an immersive, virtual 3D space) to explore studying in London. A bank enhances CX, improves data protection, and reduces costs with AI-powered digital ID verification.
SecureWorld News
JANUARY 17, 2024
The core conclusion is striking: virtually every component of the machine learning pipeline is vulnerable. RELATED: Safeguarding Ethical Development in ChatGPT and Other LLMs ] The report stresses that defenses like multi-modal training, data profiling, supply chain authentication, and behavior monitoring do help, but tradeoffs abound.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content