Tips and guidelines for making software applications GDPR compliant
Venture Beast
JANUARY 19, 2022
Developing a GDPR compliant software app can be a challenging task. Understand how to meet the requirements and ensure compliance. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
JANUARY 19, 2022
Developing a GDPR compliant software app can be a challenging task. Understand how to meet the requirements and ensure compliance. Read More.

Kitaboo
JANUARY 29, 2024
For any eBook developer, creating eBooks that meet the diverse needs of people in academic institutions can be time-consuming and complex. To help them deliver in a timely fashion, SDKs have started playing a crucial role in eBook development. Besides this, a customizable eBook SDK helps eBook developers in the following ways: 1.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Reimagining Cybersecurity Training: Driving Real Impact on Security Culture

ForAllSecure
JANUARY 31, 2023
The guide also serves as an educational resource on the latest security technologies. Therefore, the FFIEC provides guidance on financial regulations and best practices for federal supervisory agencies, as well as helping them develop exam policies for banks, savings associations, credit unions, thrifts, and other financial institutions.

SecureWorld News
JANUARY 2, 2024
It released the Space Security: Best Practices Guide (BPG) , a landmark document designed to safeguard every satellite, communication, and mission from the lurking threats of the digital unknown. Mitigating Risks, Not Replacing Requirements: The BPG acts as a supplementary tool, not a replacement for existing security standards.

SecureWorld News
NOVEMBER 1, 2022
Distributed denial-of-service (DDoS) attacks aim to overwhelm a target's application or website, exhausting the system's resources and making the target inaccessible to legitimate users. government agencies have come together to provide some guidelines in protecting against these attacks. Which is why some U.S. Which is why some U.S.

Galido
MARCH 11, 2017
Customized offshore software development has become popular for several reasons. Around 640 Global Delivery Centers were set up in 78 countries in the FY2015, of which 27% incremental GDCs were developed in India. Usually, a look at the website of the offshore software developer would reveal its public data. Enquire and Verify.
SecureWorld News
AUGUST 7, 2023
This first installment is "Safeguarding Ethical Development in ChatGPT and Other LLMs through a Comprehensive Approach: Integrating Security, Psychological Considerations, and Governance." Three key elements require our attention: security measures, psychological considerations, and governance strategies.

Kitaboo
JANUARY 12, 2024
The impacts of AI can be seen through its transformative influence on educational product development. The ultimate end goal is to align product development with educational goals while making it more engaging and personalized. AI in educational product development can be integrated to tackle various broad challenges.

CIO Business Intelligence
SEPTEMBER 7, 2023
Slowing the progression of AI may be impossible, but approaching AI in a thoughtful, intentional, and security-focused manner is imperative for fintech companies to nullify potential threats and maintain customer trust while still taking advantage of its power.

TM Forum
NOVEMBER 25, 2021
What: Developed an integrated suite for IoT platform with Blockchain in-house, giving massive IoT ecosystems a secure means of onboarding and delivering end-to-end use cases. Industries are embracing IoT for smart homes, surveillance drones, driverless cars, trains, vehicle platoons and many more applications.

SecureWorld News
MAY 5, 2024
We explored various applications of AI, tackled the strategic and ethical considerations, and emphasized the vital interplay between human expertise and automated systems. As AI technologies continue to advance, their integration into daily security protocols and strategies becomes more critical and complex.

CTOvision
JUNE 3, 2014
They have a great portfolio of technologies needed by enterprises today and are helping make mobile workforces more secure, agile and productive. I believe this acquisition by Good Technologies will result in a very significant enhancement in the ability of enterprises to secure their mobile users. – bg. From: [link].

CTOvision
JUNE 12, 2014
Why does security have to be so onerous? Is this password secure enough: Mxyzptlk? Now that’s secure – good luck remembering it! We’ve migrated to a userid-password society; as we’ve added layers of security, we password-protect each layer: PC (and now device), network, enclave, application, database, and storage (encryption).

SecureWorld News
APRIL 4, 2024
Clear guidelines on how company's information and IP assets can and cannot be utilized with AI systems are essential. Companies must align their GenAI usage with current legal and regulatory standards in the applicable jurisdictions, adapting to the rapidly changing landscape.

CIO Business Intelligence
NOVEMBER 9, 2023
The White House’s new executive order, “ Safe, Secure, and Trustworthy Artificial Intelligence ,” is poised to usher in a new era of national AI regulation, focusing on safety and responsibility across the sector. Naturally, such guidelines are only effective in encouraging innovation if they are consistently applied. But will it?

CIO Business Intelligence
APRIL 29, 2024
As organizations roll out AI applications and AI-enabled smartphones and devices, IT leaders may need to sell the benefits to employees or risk those investments falling short of business expectations. Our responsibility as CIOs is certainly to fund and empower work to develop and implement AI tools safely in our workplace.”

SecureWorld News
AUGUST 23, 2023
The addition of the 'implementation examples' are an extremely useful tool for organizations to actually implement the security controls they choose. Defending and Investigating Advanced Intrusions on Secure Email Gateways" at SecureWorld Dallas on Oct. and all over the world. Nader Zaveri – Sr. 8 (day 1 of the 2-day conference).

Dataconomy
MAY 17, 2024
One of the most recognizable trends of the early years of the 21st century has been the spread and application of AI (Artificial Intelligence) within many professional areas. Ethical concerns about data privacy, consent and security are critical particularly in AI-based applications that require lots of training data.

Galido
NOVEMBER 27, 2018
Information Technology Blog - - The 7 Step to Develop and Deploy Data Loss Prevention Strategy - Information Technology Blog. Hackercombat aims to guide the user with this guide to inform what’s new in data loss prevention systems, including cloud access security brokers. Develop Controls. Having a DLP in place.

CIO Business Intelligence
OCTOBER 2, 2023
Platform engineering is a sociotechnical discipline that has gained tremendous attention in the last year in response to the need for organizations to accelerate cloud native app development and management. Still, as the model evolves, more of a platform will be developed. Why platform engineering?

CTOvision
JANUARY 9, 2014
Eligible applicants invited to apply for nearly $5M in CRCF funds. CRCF advances science- and technology-based research, development and commercialization to drive economic growth in Virginia, strengthen collaboration and partnerships between the public and private sectors, and foster high-potential technology companies.

mrc's Cup of Joe Blog
MARCH 28, 2019
Summary: A growing trend, low-code development claims to address many of the common challenges facing businesses today. photo credit: ppokta via pixabay cc According to Forrester Research , the low-code development platform market is growing by 50% year-over-year. Not only does this waste resources, it creates security risks.

CTOvision
SEPTEMBER 26, 2016
Once an enterprise has decided to go down the path of building native mobile apps, there is one critical decision involved –whether to build these apps in-house or to outsource development. In the series, this third post will be useful when the choice has been made to develop native apps.

CIO Business Intelligence
MAY 2, 2024
As a result, Siemens Mobility learned that UiPath could help it automate processes involving different software applications, with a focus on SAP integration. “We A strategy for autonomy Siemens has three primary approaches to RPA: the initiative approach, the citizen developer approach, and robotics as a service.

Network World
MAY 16, 2017
Even though larger cloud providers offer security and implementation guidelines, companies still face significant risks and challenges when deploying secure applications to the cloud. These companies boast elite security and DevOps teams that work to secure their products and write new features.

Eric D. Brown
MARCH 5, 2024
But to harness these benefits, we must first demystify AI, peeling back the layers to understand its mechanisms, applications, and how it can be integrated into your business model for tangible results. This capability is valuable across a wide range of applications. At its core, machine learning is like educating a child.

CIO Business Intelligence
APRIL 30, 2024
The European Parliament voted in mid-March to approve the EU AI Act , the world’s first major piece of legislation that would regulate the use and deployment of artificial intelligence applications. The untargeted scraping of facial images from the internet or security footage to create facial recognition databases is also prohibited.
Dataconomy
MAY 10, 2024
One of the most recognizable trends of the early years of the 21st century has been the spread and application of AI (Artificial Intelligence) within many professional areas. Embedding ethical AI principles in development processes 1. These AI framework is little bit very complex task to understanding.

CTOvision
NOVEMBER 13, 2013
Defense Information Systems Agency (DISA) announced the awarding of a landmark contract for Mobile Device Management and Mobile Application Store (MDM/MAS) capabilities to support the use of hundreds of thousands of Apple iOS and Android devices across the U.S. Department of Defense (DoD). In partnership with Digital Management Inc. (DMI),
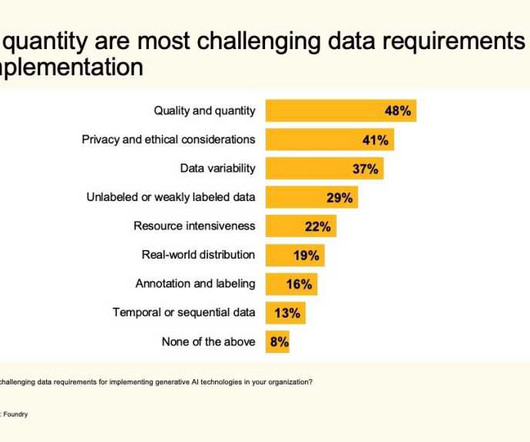
CIO Business Intelligence
OCTOBER 11, 2023
Content generation is another key use case for gen AI, cited by 55% of respondents, with industry-specific applications (48%), data augmentation (46%), and personalized recommendations (39%) rounding out the top five. Software vendors have been busy infusing generative AI into their products.

CIO Business Intelligence
AUGUST 25, 2022
The average remote worker, BYOD remote worker, power remote worker, high-security remote worker, or executives? Best Practice 4: Guidelines can be worth their weight in gold. A set of guidelines for how the employees should set up their home networks can help improve connectivity, avoid potential issues, and increase security.

SecureWorld News
JUNE 11, 2023
This article studies resilience concerning cybersecurity and provides applicable insights that organizations can use as guidelines in building immunity against evolving threats. Building strong defenses Preventing a breach is essential to cyber resilience because it reduces opportunities for attackers to exploit weaknesses.

Eric D. Brown
MARCH 5, 2024
But to harness these benefits, we must first demystify AI, peeling back the layers to understand its mechanisms, applications, and how it can be integrated into your business model for tangible results. This capability is valuable across a wide range of applications. At its core, machine learning is like educating a child.

Dataconomy
MAY 6, 2024
Grasping the concepts of machine learning, MLOps, and the crucial role of continuous software auditing through a reliable software development company can enhance decision-making capabilities, boost operational efficiency, and strengthen your competitive edge in the modern, tech-centric marketplace.

Dataconomy
MARCH 26, 2024
One of the most recognizable trends of the early years of the 21st century has been the spread and application of AI (Artificial Intelligence) within many professional areas. Ethical concerns about data privacy, consent and security are critical particularly in AI-based applications that require lots of training data.

CIO Business Intelligence
JUNE 20, 2023
To achieve these goals, IT and business executives must manage challenges across data governance, security, and compliance to protect sensitive customer, citizen, and country data using privacy, access, and security controls. For further details, check out the IDC report on sovereign cloud here.
Dataconomy
SEPTEMBER 13, 2023
Designed for developers intent on incorporating state-of-the-art conversational AI into their projects, this API transforms ordinary applications into interactive, intelligent platforms. Securing a Claude API key requires a series of straightforward steps, initiated via Anthropic’s web console. How to use Claude API key?

CIO Business Intelligence
JANUARY 31, 2024
Concerns that AI contributes to global warming stem from estimates that GPUs used to develop and keep AI models running use four times as much energy as those serving conventional cloud applications, and that AI could be on track to use as much electricity as Ireland. Think about how much computer and carbon that saved.”

ForAllSecure
FEBRUARY 2, 2023
Finding an effective way to protect applications from malicious actors can be a daunting task. Running tests manually is time-consuming, and small teams may feel that they don’t have the time required to secure their applications. Fuzz testing has traditionally only been available to companies with large security budgets.

mrc's Cup of Joe Blog
MARCH 10, 2022
Summary: Web application development is changing and becoming increasingly important. How will web application development evolve and what areas should you focus on? photo credit: lakexyde via pixabay cc We’re going to go over some of the biggest trends to watch this year in the world of web application development.
Kitaboo
APRIL 24, 2024
DRM for eBook Security and User Experience Device Compatibility Safe Transactions Personalized Recommendations IV. An extensive set of rules, policies, and guidelines help content creators and distributors implement the DRM and protect their intellectual property rights. Table of Contents I. What is DRM? How Does DRM Work?

Dataconomy
MARCH 6, 2024
For the first time , this enables iPhone users to download applications from sources other than the Apple App Store. This includes the ability to install an iOS alternative app store via a web browser, enabling you to download applications from sources beyond the Apple App Store. With the release of iOS 17.4

Dataconomy
OCTOBER 17, 2023
While these can be malicious hackers who are after our sensitive data, they can also be white hat hackers who ensure our security by monitoring us from a distance. How safe is it to leave our cyber security in the hands of a hacker? So what are the hats worn by these hackers and how do they change their methods and goals?

Scott Lowe
AUGUST 12, 2022
DNS, BGP, hardware-based security, Kubernetes, Linux—they’re all in here. Alex Neihaus provides readers with a walkthrough for adding BGP routes to AWS security groups. Gabriel Sieben ruminates on the potential dangers of Microsoft Pluton , a new security chip co-developed by Microsoft and AMD. Networking.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content