Identity and authentication in the metaverse
Venture Beast
JANUARY 26, 2022
Just as identity and authentication is pivotal to today's world, the metaverse will also require people to prove who they are. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
JANUARY 26, 2022
Just as identity and authentication is pivotal to today's world, the metaverse will also require people to prove who they are. Read More.

Kitaboo
FEBRUARY 16, 2021
The emergence of digital content and its prevalence during the pandemic has given rise to virtual textbooks. This blog post explains how virtual textbooks are different and even better than printed textbooks in many ways. How Can Publishers Benefit From Virtual Textbooks? Virtual Textbooks Are Easier to Update.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Vox
FEBRUARY 21, 2023
Friso Gentsch/picture alliance via Getty Images You used to pay for social media with your eyeballs. If you’re not paying for the product, you are the product” has long been a common refrain about the business of social media. But now, this free model of social media — subsidized by advertising — is under pressure.
GeekWire
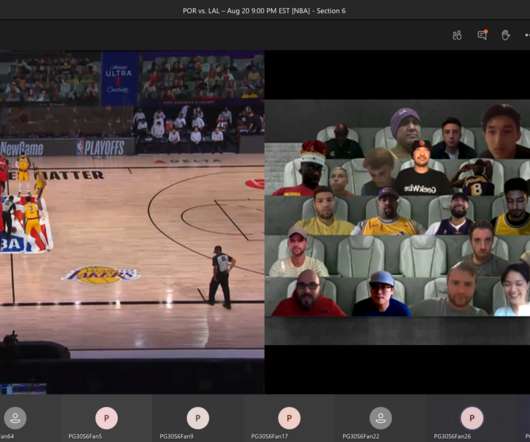
AUGUST 21, 2020
This is the spectator view for fans watching NBA games “courtside” in Microsoft Teams: the live stream on one side, and your virtual cheering section on the other. My big takeaway: Microsoft and the NBA are on to something with their new tech-fueled virtual fan experience. Look out for me in the virtual stands!!!

GeekWire
DECEMBER 18, 2020
Seattle-based FFA just wrapped up a virtual version of its eight-week Ready Set Raise program, which requires each company to have a female or non-binary CEO. FFA is a social purpose corporation , a type of profit corporation the state of Washington created in 2012, and is funded primarily through corporate partners.

The Verge
MARCH 8, 2021
Facebook’s future virtual reality headsets should capture users’ facial expressions for more realistic digital avatars, says CEO Mark Zuckerberg. In a podcast interview for The Information , Zuckerberg expounded on the next decade in virtual and augmented reality, including future Oculus VR devices.

SecureWorld News
APRIL 29, 2024
If there is a silver lining, it is likely the data exposed to advertisers such as Microsoft and Google does not include usernames, passwords, Social Security numbers (SSNs), financial account information, or credit card numbers. Authenticator apps, SMS codes, and security devices such as YubiKey are a few of the options available for MFA."

Dataconomy
JANUARY 23, 2024
Join us on a journey through the intricacies of Snapchat’s security measures, shedding light on the protection of snaps and essential safety considerations for users navigating the ever-evolving landscape of social media. Enable two-factor authentication for an added layer of security. Is Snapchat encrypted? Let’s find out!

CIO Business Intelligence
JUNE 23, 2022
Virtual Private Networks (VPNs) have long been the go-to method for providing remote users secure access to the corporate network. In 2021, Gartner saw a 127% increase in interest about ZTNA, compared to the prior year – and most of the use cases centered on ZTNA as a replacement for Virtual Private Networks (VPNs).

CIO Business Intelligence
MAY 31, 2022
The metaverse will require a digital foundation that enables trust and authenticity. Currently, society is at an inflection point as people have lower confidence in the internet and in social media. Here are five implications these technologies will have on security and privacy as we build our collective future. . Building trust.

Kitaboo
DECEMBER 27, 2023
10 Ways in Which Artificial Intelligence (AI) Can Change the Future of Content Automates Repetitive Tasks SEO Optimization Machine Translation Emotion Analysis Natural Language Processing (NLP) Fraud Detection Content Personalization Automated Transcription Services Creative Assistance Voice Recognition Through Chatbots and Virtual Assistants III.

CIO Business Intelligence
JULY 10, 2023
The BPO’s contact center blends various media streams (chat, email, voice, video, social) with self-built AI chatbots and voice bots using the Avaya Experience Platform and Google Dialogflow. Traditional identity verification methods like knowledge-based authentication (e.g. what’s your mother’s maiden name?”)

SecureWorld News
NOVEMBER 9, 2021
Bring awareness to social engineering and mitigate those risks. Social engineering, according to most experts at SecureWorld, is the key reason cyber incidents are thriving. It's clear that social engineering is the number one way that ransomware gets into people's environments," says Grimes.

Dataconomy
DECEMBER 15, 2023
The drama unfolded on social media platforms, with a Reddit thread at the epicenter, swiftly removed by moderators. OpenAI’s CEO, Sam Altman, stepped onto the virtual stage to address the chatter. Users began scrutinizing the details in the screenshot, questioning the leak’s authenticity. But the plot thickened.

Dataconomy
AUGUST 22, 2023
These technologies offer students the thrill of navigating through virtual terrains, executing tasks, and participating in simulations molded to their unique requirements. Initiatives like accruing virtual points upon task completion or indulging in friendly competition via digital leaderboards exemplify this trend.

Kitaboo
FEBRUARY 29, 2024
Advantages of Interactive eBooks Multimedia Engagement Active Learning and Participation Adaptability and Scalability Social Collaboration Enhanced Accessibility Personalized Reading Experience Engagement and Knowledge Retention Innovation and Experimentation III. Multimedia Integration Passive Interactivity vs. Active Engagement II.

Dataconomy
JULY 27, 2023
TikTok NPC streaming has become the number one agenda of social media. Welcome to a realm where reality blurs with virtuality, and social media creators are transforming into something straight out of video games. As more virtual gifts are sent to the creator, the more bizarre and over-the-top their reactions become.

Dataconomy
DECEMBER 29, 2023
In stark contrast to human influencers who gain popularity through real-life experiences, talents, or expertise, AI influencers are entirely synthetic characters designed to engage audiences on social media platforms. Social media presence: AI influencers are typically active on various social media platforms, just like human influencers.

CTOvision
OCTOBER 17, 2016
Cloud computing and cloud storage at one time was once viewed as a risky proposition for businesses; why trust an unknown virtual platform to handle business needs when everything could be safely handled onsite? One important security consideration is password and authentication management. Bob Gourley. Performance is another benefit.

SecureWorld News
JUNE 16, 2021
If someone is in your organization's Slack channel, then they are authenticated and the environment is secure. The group was able to steal the data after socially engineering an EA employee to provide login credentials over a Slack channel. RELATED: Famous Twitter Accounts Hacked: Insider Threat or Social Engineering Attack? ].

SecureWorld News
JUNE 16, 2021
If someone is in your organization's Slack channel, then they are authenticated and the environment is secure. The group was able to steal the data after socially engineering an EA employee to provide login credentials over a Slack channel. RELATED: Famous Twitter Accounts Hacked: Insider Threat or Social Engineering Attack? ].

GeekWire
AUGUST 17, 2020
Cherian Porter, lower left, and Terrell Cobb, lower right, co-founders of Black Designers at Microsoft, present their Thinkercyze virtual design challenge as part of the Seattle Design Festival (video below). the art of finding authentic solutions to challenges?and and be their authentic self.?Microsoft candidates?and

Dataconomy
JANUARY 29, 2024
Here are some detailed strategies and considerations for building trust and rapport: Be authentic and genuine : Clients can sense when an agent is sincere. Showing your authentic self helps to build a genuine connection. client meetings, property showings, administrative work).

CIO Business Intelligence
NOVEMBER 6, 2023
Show recognition According to a recent Gallup/Workhuman survey , employee recognition that is fulfilling, authentic, equitable, personalized, and embedded into the company culture is so critical to employee engagement that it can be tracked to the bottom line. You don’t even need strong social skills. Talk about it on social media.
The Accidental Successful CIO
SEPTEMBER 22, 2021
Synchrony Financial uses AI-enabled applications to speed up credit-card authentication, identify and prevent fraud, power virtual agents and personalize marketing offers. AI is a competitive advantage for them.

Kitaboo
NOVEMBER 30, 2023
You can also explore forums or social media networks to get valuable insights into the performance of such platforms. Look for features like virtual classrooms, video tools, content accessibility, access to synchronous and asynchronous content, discussion forums, and other collaborative tools.

Dataconomy
MARCH 15, 2024
Strengthen the security of your online accounts Every account you set up, whether on social media, a digital banking platform, or an e-commerce site, requires password protection. Most platforms also offer two-factor authentication that generates a random passcode each time you log in.

Dataconomy
DECEMBER 4, 2023
The core philosophy of Lunchbreak AI is to empower students to achieve their best by providing them with a virtual study buddy. The tool ensures that the content it generates is undetectable as AI-written, while also training its model on over 40,000 student essays and research papers for authenticity.
Kitaboo
FEBRUARY 21, 2024
Ensure that these can be further shared on online marketplaces, social media channels, and websites. Assess privacy settings, user authentication mechanisms, and permissions controls, and also consider the platform’s track record on data breaches and its commitment to user privacy.
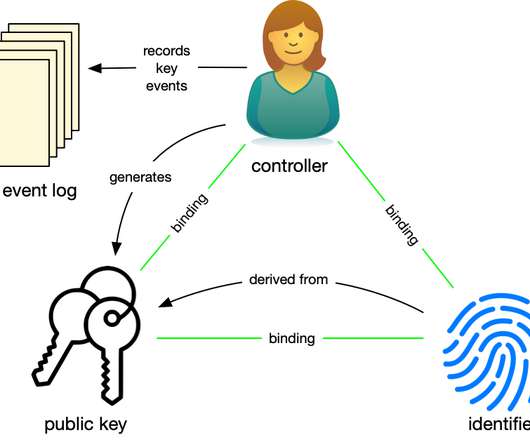
Phil Windley
JUNE 14, 2021
Summary: I'm attend the Hyperledger Global Forum this last week–all virtual. Alice) who, by virtue of knowing the authentication factors (e.g. Alice uses her private key to sign statements that authenticate herself and authorize use of the identifier. Secure - DID-based relationships are mutually authenticating.

Dataconomy
AUGUST 8, 2023
He described the profound emotional odyssey of Joshua Barbeau, a 33-year-old man who sought the assistance of Project December to construct a virtual entity, a thanabot, mirroring the personality of his late fiancée, tragically lost eight years prior.

Kitaboo
FEBRUARY 21, 2024
Digital solutions can help implement features that encourage user interaction, such as comment sections, social media integration, and personalized recommendations. User Engagement and Retention With the abundance of digital content available, retaining user attention and fostering engagement can be a constant challenge.

Dataconomy
JANUARY 15, 2024
Through a tailored social media strategy and engaging community-focused content, we managed to double their online following and increase in-store foot traffic by 40% in just six months. Revamp sentence structure for authenticity To circumvent the formulaic nature of AI writing tools, consider altering your sentence structure and syntax.

Trends in the Living Networks
JULY 2, 2012
He then describes the core idea: The social web has given birth to a new breed of creative entrepreneurs who stride the virtual globe attracting fans and picking up business, often from the comfort of their home (or more often than not, on the road somewhere). KEEP IT REAL. CREATE CONTENT … OFTEN.

Trends in the Living Networks
MARCH 11, 2012
Applying cultural intelligence allows innovators to understand how meaning is changing, especially in regard to unique aspects of trust, authenticity and progress. View more presentations from Tim Stock. Each app reflects a facet of what real thought processes actually look like in the development of meaningful ideas and connections.

Dataconomy
JUNE 20, 2023
“In the future, multipurpose generative AI models like Voicebox could give natural-sounding voices to virtual assistants and non-player characters in the metaverse. Even if two people don’t speak the same language, they might be able to converse naturally and authentically in the future thanks to this skill.
The Accidental Successful CIO
SEPTEMBER 21, 2022
CIOs at credit-card business use AI-enabled applications to speed up credit-card authentication, identify and prevent fraud, power virtual agents and personalize marketing offers. AI is a competitive advantage for these firms.

CIO Business Intelligence
JULY 17, 2023
This can occur through techniques like phishing, social engineering, or exploiting vulnerabilities in authentication mechanisms. This increased confidence, plus the ability to integrate with existing CI/CD workflows, allows teams to push effective virtual patches out faster, closing the door on attackers more quickly than ever before.

Kitaboo
JUNE 6, 2019
Provides an Opportunity to Experiment on a Virtual Platform. So, teachers found a solution where they let the students learn about the technicalities of the topic and practice on an online virtual platform. While this may or may not prove disastrous in an actual lab, it is better to experiment once virtually.

CIO Business Intelligence
APRIL 19, 2023
How do you define ‘best-in-class’ from a social perspective? Also important is DNS filtering, multifactor authentication, network automation, and generally making sure that you and your team understand your network better than the apex predators who are trying to break into it. I think about this in the context of a ‘relationship bank.’

GeekWire
JULY 21, 2020
Bring your authentic self to your role, even if you look or identify differently or have a different background than others in the room. It’s also a great alternative to social media and online shopping, both of which I’m fairly strict about limiting. Your preferred social network? Pinterest for personal use. Schedule it.

Dataconomy
SEPTEMBER 26, 2023
Whenever possible, enable two-factor authentication (2FA) for your online accounts. Be wary of sharing personal information on social media or other platforms, as hackers can use this to their advantage. Consider using a Virtual Private Network (VPN) to encrypt your internet connection and hide your IP address.

GeekWire
MAY 11, 2020
Mårten Mickos speaks with GeekWire via video chat in advance of his keynote this Thursday May 14 at the third annual Nordic Innovation Summit, a free virtual event this year. Typically taking place at the museum in Seattle’s Ballard neighborhood, it’s a virtual event this year, free to attend online. Screenshot via Zoom.).

Galido
OCTOBER 29, 2019
Both buying and selling involve negotiations after which a deal is reached with binding documents and files to prove the authenticity of the transaction. You can easily and quickly do this with a virtual data room. Businesses often involve buying from an individual or company and selling to another party.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content