Tips and guidelines for making software applications GDPR compliant
Venture Beast
JANUARY 19, 2022
Developing a GDPR compliant software app can be a challenging task. Understand how to meet the requirements and ensure compliance. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
JANUARY 19, 2022
Developing a GDPR compliant software app can be a challenging task. Understand how to meet the requirements and ensure compliance. Read More.

ForAllSecure
JANUARY 31, 2023
The resource guide is a valuable tool for financial institutions of all sizes as it provides best practices, recommendations, and resources to help organizations protect their networks and data from cyber threats. The guide also serves as an educational resource on the latest security technologies.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureWorld News
NOVEMBER 1, 2022
Distributed denial-of-service (DDoS) attacks aim to overwhelm a target's application or website, exhausting the system's resources and making the target inaccessible to legitimate users. government agencies have come together to provide some guidelines in protecting against these attacks. Which is why some U.S. Which is why some U.S.

Tech Republic Security
SEPTEMBER 13, 2023
The purpose of this policy from TechRepublic Premium is to provide guidelines for the proper use of peer-to-peer file sharing. It includes an authorization form for approval of P2P file transmission, which sets the conditions and parameters in which this data exchange must occur.

Advertisement
Every data-driven project calls for a review of your data architecture—and that includes embedded analytics. Before you add new dashboards and reports to your application, you need to evaluate your data architecture with analytics in mind. Expert guidelines for a high-performance, analytics-ready modern data architecture.

The Verge
AUGUST 6, 2020
And now we know exactly why: Apple won’t allow those products, because of strict App Store guidelines that make cloud services like xCloud and its competitor, Google Stadia, effectively impossible to operate on the iPhone. Apple is pretty explicit about all of this in the App Store guidelines, specifically section 4.2.7:

CIO Business Intelligence
JANUARY 24, 2024
Organizations can’t afford to mess up their data strategies, because too much is at stake in the digital economy. How enterprises gather, store, cleanse, access, and secure their data can be a major factor in their ability to meet corporate goals. Here are some data strategy mistakes IT leaders would be wise to avoid.

CIO Business Intelligence
AUGUST 5, 2022
And at its core is the need to secure customer data through a robust set of requirements. The regulations streamline how entities who handle customer banking information will secure their systems and share details within protected application program interfaces. Securing customer data.

CIO Business Intelligence
MARCH 24, 2023
Data governance definition Data governance is a system for defining who within an organization has authority and control over data assets and how those data assets may be used. It encompasses the people, processes, and technologies required to manage and protect data assets.

CIO Business Intelligence
NOVEMBER 14, 2022
Decision support systems definition A decision support system (DSS) is an interactive information system that analyzes large volumes of data for informing business decisions. A DSS leverages a combination of raw data, documents, personal knowledge, and/or business models to help users make decisions. Data-driven DSS.

CIO Business Intelligence
APRIL 19, 2023
Most organizations are already well under way with their digital transformation journeys, particularly data modernization. For most companies, the drive for data modernization is attributed to the massive growth of data and a business goal to harness as much data as possible to unlock its potential in transformative ways.

KineticData
DECEMBER 28, 2022
Kinetic Data’s secure workflow automation platform and data ingestion capabilities will be utilized to help protect digital information for Department of Defense (DoD) personnel. For Kinetic, the unique applicant tracking system requires a sturdy integration approach to ingest personnel data from a variety of unclassified sources.

CIO Business Intelligence
JULY 13, 2022
In a previous article , we talked about the need for organizations to secure data wherever it resides. The complexity of today’s supply chains brings that need into sharp focus, while highlighting some of the challenges of successfully protecting data. Don’t forget internal applications. The bottom line? Securing the cloud.

SecureWorld News
APRIL 4, 2024
Understanding the impact GenAI technologies possess the dual ability to consume and generate IP, encompassing content, data, and processes. Clear guidelines on how company's information and IP assets can and cannot be utilized with AI systems are essential. This dual capability has profound implications for IP ownership and protection.

Galido
MARCH 11, 2017
Before discussing the guidelines to find the best offshore software development company, let’s discuss briefly the reasons to outsource. Specialized knowledge about various business segments teamed with technical knowledge help in custom application development. Outsourcing to can reduce overall IT project cost to almost 30-40%.

CIO Business Intelligence
MARCH 29, 2024
Another genAI assistant developed by Rocket analyzes applicants’ employer names to ensure that employers that could be entered under various names are understood to be one and the same, vastly speeding up the decision-making process. For example, most people know Google and Alphabet are the same employer.

Eric D. Brown
MARCH 5, 2024
But to harness these benefits, we must first demystify AI, peeling back the layers to understand its mechanisms, applications, and how it can be integrated into your business model for tangible results. Generally, the more data it analyzes, the better it recognizes patterns and makes accurate predictions.

CIO Business Intelligence
APRIL 25, 2024
Few companies operate at the scale that LinkedIn does or have access to similar troves of data. But when it came to delivering data to LinkedIn’s customers, costs exploded. On the flip side, some job applicants post poorly phrased histories that do not effectively reflect their wealth of experience in problem-solving, for example.

CIO Business Intelligence
JUNE 21, 2022
OCI Dedicated region, which started off as a service to enable enterprises to take advantage of cloud technology inside their data centers while complying with data residency and other regulatory guidelines, offers a portfolio of public cloud services along with Oracle Fusion SaaS applications. .

CIO Business Intelligence
JANUARY 31, 2024
Everything from geothermal data centers to more efficient graphic processing units (GPUs) can help. Rather than training the model on all the training data at once, Salesforce trains the model in multiple “epochs” in which a portion of the data is slightly modified in each one based on the results of the earlier training.

Eric D. Brown
MARCH 5, 2024
But to harness these benefits, we must first demystify AI, peeling back the layers to understand its mechanisms, applications, and how it can be integrated into your business model for tangible results. Generally, the more data it analyzes, the better it recognizes patterns and makes accurate predictions.

CIO Business Intelligence
JULY 13, 2022
In a bid to help enterprises and institutions in the European Union navigate data privacy, residency, and other regulatory guidelines, Oracle plans to launch two sovereign cloud regions for the European Union this year.

CIO Business Intelligence
NOVEMBER 9, 2023
government’s opening salvo in creating a comprehensive regulatory framework for AI, applicable both in the federal government and the private sector. Protecting consumer privacy The AI Executive Order also calls to protect consumer privacy by creating guidelines for agencies to assess privacy techniques used in AI. But will it?

Tech Republic Big Data
MAY 30, 2023
The purpose of this policy from TechRepublic Premium is to provide guidelines for the appropriate retention and disposal of physical and electronic documents. The post Document retention policy appeared first on TechRepublic.

CIO Business Intelligence
APRIL 30, 2024
The European Parliament voted in mid-March to approve the EU AI Act , the world’s first major piece of legislation that would regulate the use and deployment of artificial intelligence applications. The transparency and monitoring requirements will be a new experience for some organizations, Domino Data Lab’s Carlsson says.

SecureWorld News
SEPTEMBER 1, 2023
Shadow AI refers to AI tools or applications that are used within an organization without explicit approval or oversight. Regardless of the intention—whether benign or malicious—Shadow AI presents risks ranging from data breaches to skewed business decisions.

TM Forum
NOVEMBER 11, 2021
The Catalyst is championed by Telefónica and American Tower Corporation, with NTT Data as prime system integrator and supported by participants Akamanta, Blue Prism, Compax Software Development, MATRIXX Software, and Salesforce. including for production implementation guidelines and the. Application Framework (TAM).
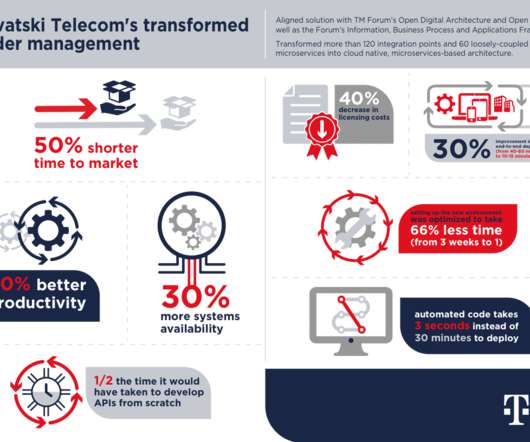
TM Forum
OCTOBER 26, 2021
The entire open-source order management stack was written from scratch, including key applications like order capture, order execution, product catalog, asset management, user documentation, notifications and more. also known as SID or GB922) data model, product catalog and interface specifications. Application Framework.

Dataconomy
MARCH 26, 2024
One of the most recognizable trends of the early years of the 21st century has been the spread and application of AI (Artificial Intelligence) within many professional areas. The data analysis, pattern recognition, and decision-making functionalities in AI have produced remarkable efficiencies and ideas.

CIO Business Intelligence
DECEMBER 19, 2022
Why Cloud Platforms Matter to Marketing Leaders According to IDC, 89% of marketing campaign management applications in Europe are now cloud based rather than on premises. Marketing is becoming digitally transformed through the adoption of new cloud-based marketing applications. A remote and home working ethos amplifies this problem.

CTOvision
JANUARY 9, 2014
Eligible applicants invited to apply for nearly $5M in CRCF funds. Applicants must submit a Letter of Intent (LOI) by Friday, January 31, 2014 to be eligible to submit an application; applications are due by Friday, February 21. Questions regarding this solicitation should be directed to crcf@cit.org.

TM Forum
NOVEMBER 25, 2021
Industries are embracing IoT for smart homes, surveillance drones, driverless cars, trains, vehicle platoons and many more applications. Jio’s platform is designed with a highly scalable architecture so that third-party applications can easily be integrated. Jio IoT Platform manages connectivity.

CIO Business Intelligence
SEPTEMBER 7, 2023
Misinformation and manipulation of data. As AI becomes more powerful, its ability to manipulate data is increasing and making it difficult to stem the tide of misinformation. Additionally, related issues during use are risk of hallucinations and prompt engineering.

CIO Business Intelligence
MAY 16, 2023
The software provider plans to do that by enhancing existing tools for estimating greenhouse gas emissions due to an enterprise’s activities, and adding capabilities for exchanging that data with partners, bringing it all together in a “green ledger” that will record the climate cost of doing business alongside the financial cost.

Dataconomy
APRIL 24, 2024
Understanding proxy servers for SEO tools Proxy servers play a vital role in search engine optimization (SEO) by enabling marketers to gather data, perform keyword research, and automate tasks without being detected or blocked by search engines.

Galido
NOVEMBER 27, 2018
Information Technology Blog - - The 7 Step to Develop and Deploy Data Loss Prevention Strategy - Information Technology Blog. It is not that only large enterprise should worry about Data Loss Prevention because now even small companies of all sizes are the target for hackers. Set Your Data on Priority. Know what Data is at Risk.

CIO Business Intelligence
JUNE 20, 2023
To achieve these goals, IT and business executives must manage challenges across data governance, security, and compliance to protect sensitive customer, citizen, and country data using privacy, access, and security controls. Data has become both a business and national asset.

TM Forum
APRIL 12, 2022
The problem CSPs face as they adopt cloud-native technologies is that a containerized, cloud-native application may work well in isolation, but be unable to automatically communicate its functionality to other applications, or to transmit what it itself needs to operate.

GeekWire
SEPTEMBER 25, 2023
Neum AI, a platform designed to assist companies in maintaining the relevancy of their AI applications with the latest data. YC received more than 24,000 applications for this year’s summer batch. Generative AI applications continue to change as new use cases are developed.

Dataconomy
JUNE 16, 2023
Gamma AI is a great tool for those who are looking for an AI-powered cloud Data Loss Prevention (DLP) tool to protect Software-as-a-Service (SaaS) applications. Any organization’s cybersecurity plan must include data loss prevention (DLP), especially in the age of cloud computing and software as a service (SaaS).

CIO Business Intelligence
APRIL 24, 2023
The European Data Protection Board (EDPB) wants to set up a task force to take a closer look at AI tools like ChatGPT, which is being interpreted as an indication that European data protection officers could set stricter rules for the use of AI. The Italian data protection authorities in particular got a head start a few weeks ago.
Kitaboo
FEBRUARY 27, 2024
Besides providing a convenient point from which the eBook can be disseminated, the distribution platform also helps in reaching a wider audience and procuring data related to the eBook sales. What operating systems, browsers, and software applications does the platform support? In how many countries will the book be accessible?

SecureWorld News
JANUARY 2, 2024
Let's blast off and explore the highlights: Universal Applicability: Whether you're building a Mars Rover or sending data from the furthest reaches of the cosmos, this BPG applies to all NASA missions, programs, and projects. But what exactly does this guide offer, and why should you care?

CIO Business Intelligence
AUGUST 25, 2022
Best Practice 4: Guidelines can be worth their weight in gold. A set of guidelines for how the employees should set up their home networks can help improve connectivity, avoid potential issues, and increase security. These guidelines can be made specific for a small set of recommended hardware.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content