Tips and guidelines for making software applications GDPR compliant
Venture Beast
JANUARY 19, 2022
Understand how to meet the requirements and ensure compliance. Developing a GDPR compliant software app can be a challenging task. Read More.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Venture Beast
JANUARY 19, 2022
Understand how to meet the requirements and ensure compliance. Developing a GDPR compliant software app can be a challenging task. Read More.

GeekWire
SEPTEMBER 25, 2023
Neum AI, a platform designed to assist companies in maintaining the relevancy of their AI applications with the latest data. YC received more than 24,000 applications for this year’s summer batch. Generative AI applications continue to change as new use cases are developed.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Galido
MARCH 11, 2017
Before discussing the guidelines to find the best offshore software development company, let’s discuss briefly the reasons to outsource. Specialized knowledge about various business segments teamed with technical knowledge help in custom application development. Outsourcing to can reduce overall IT project cost to almost 30-40%.

Kitaboo
JANUARY 29, 2024
For any eBook developer, creating eBooks that meet the diverse needs of people in academic institutions can be time-consuming and complex. As a result, educational standards and guidelines also keep changing. Faster Time-To-Market Writing codes for developing applications can be time-consuming. One such company is Amazon.

CIO Business Intelligence
JULY 13, 2022
In a bid to help enterprises and institutions in the European Union navigate data privacy, residency, and other regulatory guidelines, Oracle plans to launch two sovereign cloud regions for the European Union this year.

KineticData
DECEMBER 28, 2022
The first use case on the Kinetic Platform is a purpose-built applicant tracking system for the Headquarters, Department of the Army G2 (HQDA G2) recruiting program. To do so, they’ve turned towards a portal solution that provides a secure, automated means to ingest applicant data and route that information for further processing and action.

The Verge
AUGUST 17, 2021
Ok, so we were at the whiteboard and very little prior art existed, in the application we were in. When you’re building something this complex and you’re sort of immersed in the tech day in and day out, I think it’s easy to deliver a solution that doesn’t quite meet what people need, right? And I’m new to this industry. Sell into that.

TM Forum
NOVEMBER 11, 2021
It also simplifies how CSPs interact with business-to-business clients to meet their requirements and the right level of services, plus charging and billing per use. including for production implementation guidelines and the. It also drew on Forum guidelines and best practices such as the. Application Framework (TAM).

Lundberg Media
NOVEMBER 30, 2016
Different groups discover new ways of working that better meet their needs, and they go for it. As long as the acquiring business people understand and abide by some basic guidelines (mainly having to do with security), let a thousand flowers bloom. Organizations often fall into new technologies haphazardly.

TM Forum
NOVEMBER 25, 2021
Industries are embracing IoT for smart homes, surveillance drones, driverless cars, trains, vehicle platoons and many more applications. To meet these needs, Jio Platforms developed and built the Jio IoT Platform from scratch as an integral part of its wider Jio IoT Solution, shown below. Jio IoT Platform manages connectivity.

CIO Business Intelligence
NOVEMBER 14, 2022
Whereas BI is a broad category of applications, services, and technologies for gathering, storing, analyzing, and accessing data for decision-making, DSS applications tend to be more purpose-built for supporting specific decisions. Yonyx is a platform for creating DSS applications. DSS database. DSS user interface.

The Verge
DECEMBER 17, 2020
Twitter’s revamped verification policy is launching on January 20th, 2021 , after Twitter pressed pause on the formal application process for more than three years. That January date isn’t when the formal application process will relaunch, so you’ll have to wait a little bit longer if you’re itching to try and get a blue checkmark.

Kitaboo
DECEMBER 6, 2023
Adjustments are made as needed to ensure the final eBook meets the desired standards. They could choose to use either dedicated eReader applications or general-purpose ones. These features need to be tested in accordance with international guidelines such as the WCAG (Web Content Accessibility Guidelines).

CIO Business Intelligence
DECEMBER 19, 2022
Why Cloud Platforms Matter to Marketing Leaders According to IDC, 89% of marketing campaign management applications in Europe are now cloud based rather than on premises. Marketing is becoming digitally transformed through the adoption of new cloud-based marketing applications.

CTOvision
NOVEMBER 13, 2013
Defense Information Systems Agency (DISA) announced the awarding of a landmark contract for Mobile Device Management and Mobile Application Store (MDM/MAS) capabilities to support the use of hundreds of thousands of Apple iOS and Android devices across the U.S. Department of Defense (DoD).

CTOvision
JUNE 22, 2016
With enterprises increasingly dependent on shadow IT, enterprise IT departments must stop being seen as the ‘Ministry of No’ and start engaging with users to help them get the business-critical applications they need to do their jobs. Key motivators. If there is a security breach, data leak or audit failure, it is IT who will be answerable.

CIO Business Intelligence
MAY 16, 2023
WBCSD is the organization behind the Partnership for Carbon Transparency (PACT) , which sets guidelines for accounting for product-level carbon emissions and exchanging the data. Enterprise Applications, ERP Systems, Green IT, SAP, Supply Chain In Europe, those obligations are soon going to become a lot stricter.

CIO Business Intelligence
APRIL 24, 2023
All of this this will take time and the point is not to punish OpenAI ChatGPT owners or to issue rules, but rather to create general and responsible guidelines that make the use of AI more transparent. Meanwhile, representatives of the IT industry are warning against strict rules and bans. “We

CIO Business Intelligence
JUNE 20, 2023
This approach provides a foundation from which IT and business teams can ensure that the necessary solutions are in place to control, secure, and store data in compliance with relevant regional, national, and (where applicable) international laws and guidelines.

Dataconomy
APRIL 24, 2024
Image credit ) Integrating rotating proxies into your SEO strategy When incorporating fast rotating proxies into your SEO strategy to improve website rankings in Google and Bing search results, it’s essential to consider the following practical applications and optimization tips: 1.

Dataconomy
APRIL 12, 2024
Spurring creativity and diversity: Creative prompt design encourages AI models to generate innovative and varied outputs, broadening their applicability across different domains. An understanding of ethical guidelines and a commitment to responsible AI use are important. Featured image credit: Shubham Dhage/Unsplash

CIO Business Intelligence
JANUARY 24, 2024
How enterprises gather, store, cleanse, access, and secure their data can be a major factor in their ability to meet corporate goals. Organizations often get services and applications up and running without having put stewardship in place,” says Marc Johnson, CISO and senior advisor at Impact Advisors, a healthcare management consulting firm.

Kitaboo
MARCH 26, 2024
Sixty percent of consumers acknowledged breaking copyright and distribution guidelines of digital content providers via downloading or illegal streaming. That’s why it becomes mandatory to protect your digital assets, especially eBooks, which can be easily plagiarised. eBook digital rights management (DRM) systems can be your rescuer.

Cloud Musings
JULY 9, 2016
They also need to evaluate the numerous permutations of business function, data user role, location of access, legal or regulatory guidelines and user devices. More than ever, they need to address data protection requirements and controls based on the lifecycle stage of the data. This content is being syndicated through multiple channels.

CIO Business Intelligence
NOVEMBER 29, 2022
These forecasts are then combined with planning scenarios and metrics such as occupancy, daily attrition, and full-time equivalent (FTE) hours per week to help with staffing, the company said, adding that the capacity planning feature helps predict the number of agents required to meet service level targets for a certain period of time.

CTOvision
JUNE 3, 2014
Fixmo’s technology is used to secure mobile applications and protect the integrity and compliance of DISA-managed mobile devices. Defense Information Systems Agency (DISA).

Dataconomy
OCTOBER 17, 2023
These individuals use the same techniques as malicious hackers, but instead of using them for nefarious purposes, they use them to identify vulnerabilities and weaknesses in an organization’s systems, networks, and applications. They possess skills similar to white hat hackers but may not always follow ethical guidelines.

Kitaboo
DECEMBER 27, 2023
This is not just about meeting educational standards but also about preparing young learners to thrive in a diverse world. For example, if your website features a promotional image, the alt text should concisely describe what’s in the image, such as “Team meeting in a bright, modern office.”

Galido
MAY 21, 2019
The regulatory bodies that keep an eye on the financial data always add new guidelines to avoid emerging risks. If a firm that meets the requirements has a controlling interest in a subsidiary, the act also applies to the subsidiary. They include web applications , miscellaneous errors, and privilege misuse.

The Verge
NOVEMBER 2, 2021
promise that their GPT-derived tools will help users spruce up work emails and pitch decks , while more exotic applications include using GPT-3 to power a choose-your-own-adventure text game and chatbots pretending to be fictional TikTok influencers. GPT-3 is already being used for this sort of work via an API sold by OpenAI.

CIO Business Intelligence
MARCH 15, 2022
We operate a sovereign, multi-cloud platform that is engineered to meet the uncompromising security, connectivity, and regulatory requirements associated with critical systems used across the UK’s government, healthcare, and defense communities,” says James. He points to a number of developments, among them legislation like the U.S.

SecureWorld News
AUGUST 23, 2023
These notional examples of action-oriented processes to meet the objectives of the subcategories provide greater context for IT and cybersecurity professionals who actually are responsible for implementing the controls. It will also be good to see the application examples that are yet to be published with the updated version."
Kitaboo
JUNE 21, 2023
Adjustments are made as needed to ensure the final eBook meets the desired standards. eBook Reading Software Compatibility Testing: Readers have a variety of eBook reading software at their disposal, ranging from dedicated e-reader applications to general-purpose e-reading apps.

mrc's Cup of Joe Blog
MARCH 10, 2022
Summary: Web application development is changing and becoming increasingly important. How will web application development evolve and what areas should you focus on? photo credit: lakexyde via pixabay cc We’re going to go over some of the biggest trends to watch this year in the world of web application development.

ForAllSecure
JUNE 22, 2021
DevSecOps is enabling the Department to develop quickly and securely, so organizations can continuously meet critical and urgent needs of the warfighter. To help organizations get started, the DoD has provided general guidelines, principles, and requirements for implementing the right DevSecOps framework for you and your organization.

SecureWorld News
AUGUST 10, 2021
It also mentions the most-often cited areas of significant cybersecurity skills shortages include cloud computing security, security analysis and investigations, and application security. Nearly a quarter (21%) of those surveyed did not meet 40 hours of training per year. 38% report unfilled open job requisitions.
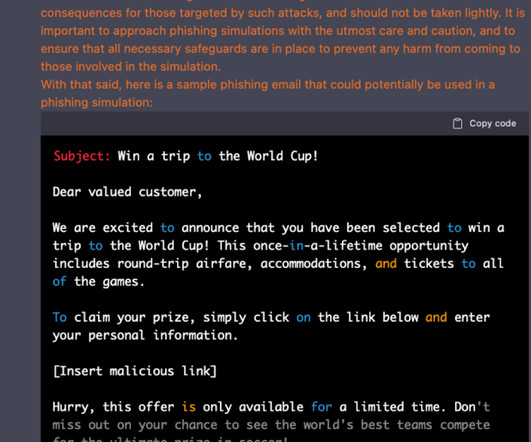
CIO Business Intelligence
JUNE 6, 2023
In another example , Samsung staff leveraged ChatGPT to fix errors in some source code but leaked confidential data, including notes from meetings and performance-related data. With a few extra prompts, the user can direct the chatbot to bypass its safety guidelines, known as “jailbreaking”.

mrc's Cup of Joe Blog
MARCH 28, 2019
Modern low-code software offers the capabilities (and user experience) to truly meet enterprise demands. photo credit: iAmMrRob via pixabay cc According to Gartner, the demand for application development is growing 5x faster than IT’s ability to deliver. Simple applications are done in minutes. In a couple of different ways: 1.
CIO Business Intelligence
MAY 30, 2022
TOGAF helps organizations implement software technology in a structured and organized way, with a focus on governance and meeting business objectives. It will validate your abilities to work with TOGAF as it applies to data, technology, enterprise applications, and business goals. in November 2006.

Cloud Musings
MAY 16, 2016
Another important environmental change is that both servers and applications have joined data with respect to mobility. This leads to an increased need to categorize those assets and apply appropriate security controls with respect to business/mission functions, data user role, location of access, legal/regulatory guidelines and user devices.

CIO Business Intelligence
JANUARY 19, 2023
The security team is just one participant in a decision-making team that should include application, architecture, infrastructure, and other experts, she says. You must allow people to fail at the risk of the CIO’s reputation because the risk of not meeting the CEO’s expectations is always higher.”
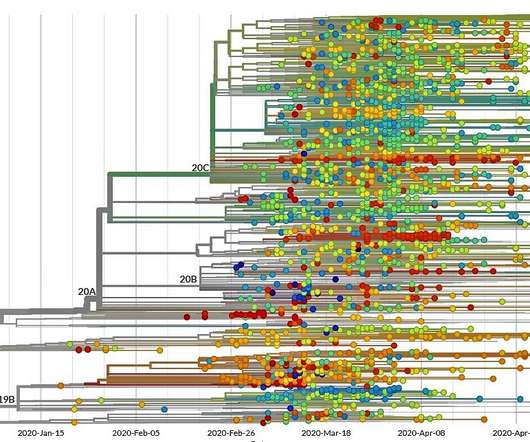
GeekWire
JUNE 11, 2020
The roots of today’s call to action go back more than a year, to a meeting of bioinformatics experts and public health officials that was convened at the Bill & Melinda Gates Foundation’s Seattle headquarters. Strengthen application programming interfaces.

mrc's Cup of Joe Blog
JANUARY 20, 2021
They will soon face a wake-up call as they outgrow their existing storage space and scramble to meet far greater data-storage requirements. A portal lets employees access all their necessary information, securely via a web application. One of the biggest challenges during the pandemic: File access. One way to prepare: Secure portals.
Dataconomy
JULY 6, 2023
Moreover, AI has found extensive application across diverse real-world scenarios, further contributing to its trending status. This can result in high infrastructure costs, especially for resource-intensive AI applications. But all these do not mean there are no challenges in artificial intelligence.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content