What you need to know about Okta’s security breach
CIO Business Intelligence
OCTOBER 25, 2023
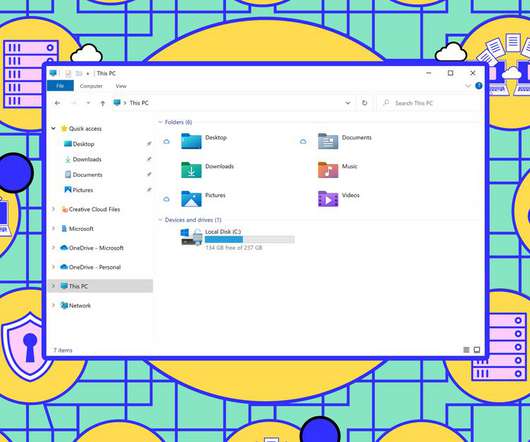
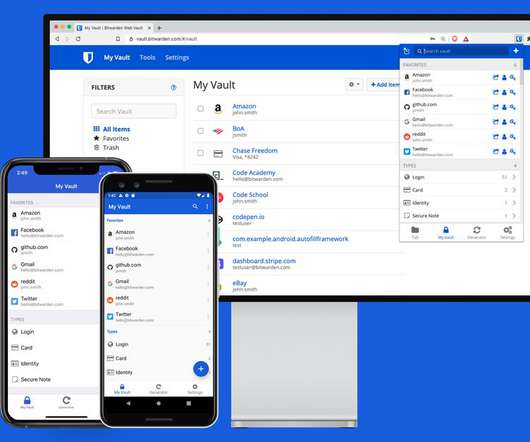
Kill chain Attack technique Deception defense Initial Access Uses stolen/purchased credentials to access internet-facing applications like IdPs, VPNs, RDP, and VDI. Creates decoys of internet-facing applications like IdPs, VPNs, and Citrix servers that attackers are very likely to target. Plants decoy credentials in Windows memory.















































Let's personalize your content