How to Balance Disaster Recovery, Backup Systems, and Security
Information Week
APRIL 22, 2024
Dale Zabriskie, field CISO with Cohesity, and Kim Larsen, CISO with Keepit, discuss ways disaster recovery can work more closely with security.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Information Week
APRIL 22, 2024
Dale Zabriskie, field CISO with Cohesity, and Kim Larsen, CISO with Keepit, discuss ways disaster recovery can work more closely with security.

Forrester IT
OCTOBER 28, 2021
Join other disaster recovery and technology resilience leaders in sharing your strategy for addressing local and systemic risks affecting your business. Click on the link below to fill out the Forrester and Disaster Recovery Journal’s biannual survey.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IT Toolbox
JULY 26, 2023
Good system administrators can handle data security, disaster recovery, communications, scalability, vendor relations, and more. The post 7 Ways a System Administrator Directly Impacts Your Business appeared first on Spiceworks.

SecureWorld News
OCTOBER 10, 2023
Being prepared for a bad situation that might never happen is better than experiencing a disaster that catches you off-guard. Read this post to learn more about disaster recovery and discover the best practices that you should apply to improve the protection of your data and IT environment. What is disaster recovery?

CIO Business Intelligence
DECEMBER 20, 2022
Investing in a robust disaster recovery program upfront can save considerable costs down the road. According to FEMA, nearly a quarter of businesses never re-open following a major disaster—a sobering statistic. [i] Without a robust disaster recovery plan in place, it can take days, weeks, or even months to recover.

Information Week
SEPTEMBER 12, 2019
In an era when systems and applications are dispersed throughout the enterprise and the cloud, IT leaders have to rethink their disaster recovery plans.
CIO Business Intelligence
SEPTEMBER 23, 2022
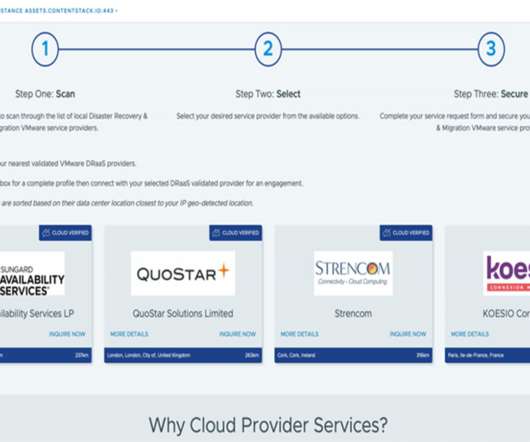
Cloud Provider Services capability enables you to choose your ideal, closest Disaster Recovery and Migration partner based on your vSphere console IP location and the nearest Disaster Recovery partner data center. Cloud Computing, Disaster Recovery, IT Leadership

SecureWorld News
NOVEMBER 3, 2022
This is the gist of a new report titled " A New Age of Disaster Recovery Planning for SMEs " (download required) produced by MIT Technology Review Insights and sponsored by OVHcloud. A disaster-recovery plan is no longer an option for SMEs; it's a must-have. SMEs are becoming more frequent targets of cyberattacks.

IT Toolbox
OCTOBER 23, 2017
Hurricanes, earthquakes, and other natural and man-made disasters create situations that demand a solid business continuity (BC)/disaster recovery (DR) plan in case of serious interruptions to your organization’s business. The year 2017 has been a busy year for hurricanes

Computer Weekly
DECEMBER 12, 2016
In this concluding part of a two-part series, Computer Weekly looks at ways of testing disaster recovery plans, with methods including array-based replication and hypervisor-based approaches

SPF13
OCTOBER 4, 2012
The Biggest Myths Surrounding Disaster Recovery. There are a variety of reasons businesses either do not have a disaster recovery plan or their current plan is substandard. This is problematic when the decision-makers have bought into one or more of the common myths surrounding disaster recovery.

Eric D. Brown
MARCH 9, 2015
If there was one time that a data center and an IT group absolutely need to be agile, it would be the time immediately after a disaster strikes. Disaster recovery planning is a challenge for every organization. The challenge for most organizations comes with the ‘how’ and the ‘when’ in disaster recovery planning.

SPF13
OCTOBER 3, 2012
There are a variety of reasons businesses either do not have a disaster recovery plan or their current plan is substandard. This is problematic when the decision-makers have bought into one or more of the common myths surrounding disaster recovery. Myth – Disaster Recovery is Expensive and Resource Intensive.

Eric D. Brown
JANUARY 28, 2015
In years past, companies have relied on multiple data center locations to act as their main disaster recovery (DR) systems and data in case of disaster. This has generally worked well for those companies that have planned and tested their DR systems and plans appropriately.

CIO Business Intelligence
MARCH 12, 2024
It’s common knowledge among CIOs that disaster recovery investments are always de-prioritized by company boards — until disaster strikes. But disaster recovery is just one example of projects that are of an important and preemptive nature that CIOs want to fund but find de-prioritized when it comes to budget approval.

Galido
JUNE 13, 2019
Information Technology Blog - - What is the Difference Between Business Continuity & Disaster Recovery? Almost everyone now is thinking about measures to mitigate disaster and to recover from the effects. It always makes a lot of sense to be prepared for disasters. Understanding Disaster Recovery.

CTOvision
FEBRUARY 26, 2014
The International Association of Cloud and Managed Service Providers (MSPAlliance), today announced that Agility Recovery would leverage the Unified Certification Standard audit (UCS) for Cloud and Managed Service Providers (MSPs) for its disaster recovery program.

All Things Distributed
NOVEMBER 26, 2013
As AWS expanded to 9 distinct AWS Regions and 25 Availability Zones across the world during the last few years, many of our customers started to leverage multiple AWS Regions to further enhance the reliability of their applications for disaster recovery.

Network World
DECEMBER 6, 2016
Whether the disaster is a flood, a power outage or human error, IT departments have the critical role of getting business systems working again. And that requires reliable disaster-recovery software. Also on CSO: Lessons from high-profile IT failures ].

Network World
MARCH 13, 2017
Dark disaster recovery vs. active architecture. Will the cost of an active-active system outweigh the potential loss of business from an outage? Asynchronous vs synchronous. Active/active vs. active/passive. No setup is objectively better or worse than another. What level of availability does your company need?

Mick's IT Blog
MAY 12, 2020
During this process, we needed to be able to differentiate what servers were on our disaster recovery VMWare server, and what servers were on the production VMWare server. During the COVID19 pandemic, one of my projects has been to build a new configuration manager server at our newer production site for optimal performance.

CIO Business Intelligence
MARCH 5, 2024
Data is the lifeblood of modern business operations, which must be able to go on significant interruption in the face of accidental deletion, data corruption and systems failure. And in case of disaster — flood, fire, earthquake or ransomware — IT needs to be able to get the business back online with all of its data as quickly as possible.

Data Center Knowledge
MARCH 19, 2014
It’s time to give up on incrementally improving a broken backup system, and instead move forward toward a new model for data protection. The cloud holds much more potential than a cheap dumping ground for backup and archive data, writes Andres Rodriguez of Nasuni. Industry Perspectives'

Network World
JULY 8, 2021
If your computing environment is subject to a large ransomware attack, you will most certainly be enacting your disaster recovery (DR) plan. But before you begin restoring systems, you must first ensure you have stopped the infection, identified it, and removed it. To read this article in full, please click here

Data Center Knowledge
JANUARY 24, 2014
SunGard Data Systems will split off its Availability Services business, which operates its data centers and disaster recovery business. Disaster Recovery SunGard Availability'

CIO Business Intelligence
MARCH 18, 2024
Cyber attacks and data breaches can wreak havoc on a business’ IT systems, resulting in massive costs to fix the damage and a long-lasting impact on customers that could hamper a company’s growth for years to come. Implement ICT security tools and processes: Any DORA-focused preparations need to take tools and processes into account.

Tech Republic
JULY 20, 2022
Jack Wallen tests the Acronis Cyber Protect Home Office app, a disaster recovery tool anyone can use to create a full disk clone of crucial systems with ease. The post Acronis Cyber Protect Home Office: The full image backup tool to meet today’s demanding needs appeared first on TechRepublic.

Tech Republic Cloud
AUGUST 11, 2022
Often used to supplement internal storage systems with scalable public cloud storage, or to streamline data backup processes and disaster recovery (DR) planning, hybrid cloud storage’s use cases are many.

CIO Business Intelligence
MAY 23, 2023
There were regional electrical outages and communications disruptions, and systems failed. We went into disaster recovery failover mode, with everyone in IT focused on getting systems back up and running. It’s a vivid memory because I was the CIO of an area financial institution at that time.

CIO Business Intelligence
NOVEMBER 18, 2022
You’ve done everything a smart and responsible organization needs to do to safeguard your systems, networks, data, and other assets from cyber threats. Furthermore, cyber-attacks have become increasingly sophisticated and commonplace, and a 5-year-old disaster recovery plan may not cover modern scenarios.

CIO Business Intelligence
DECEMBER 7, 2023
A business continuity plan is not the same as a disaster recovery plan , which focuses on restoring IT infrastructure and operations after a crisis. Because restoring IT is critical for most companies, numerous disaster recovery solutions are available. You can rely on IT to implement those solutions.

SecureWorld News
JUNE 11, 2023
In today's world of advanced digital systems, cybercriminals' attacks have mounted, putting organizations from all sectors at significant risk if they don't act proactively against them. Cyber resilience is essential: it is the capacity to anticipate and plan recovery from Adverse Cyber Events or even adapt seamlessly after the occurrence.

Data Center Knowledge
APRIL 1, 2014
As it splits from SunGard Data Systems, the company is asserting its independence while maintaining the continuity of the most familiar brand in disaster recovery. Sungard Availability Services is now an stand-alone company. Featured'

CIO Business Intelligence
JUNE 1, 2022
In what’s quickly becoming the de facto benchmarking standard for HPC storage, the IO500 named several Dell-based systems including those from CSIRO in Australia, Simon Fraser University in Canada, and Stanford University in the US. The Dell-powered system supports departmental and sponsored research across the campus.

Cloud Musings
DECEMBER 8, 2014
But when it comes to disaster recovery in the cloud, is that necessarily the case? In theory, most cloud services offer extremely resilient platforms and a modicum of disaster recovery is built in. In theory, most cloud services offer extremely resilient platforms and a modicum of disaster recovery is built in.

Network World
JANUARY 12, 2018
As we swerve onto the runway in 2018, IT leaders are finding themselves under increased pressure to ensure security, high availability and disaster recovery for the applications and systems under their care. The results of several surveys underscore the concerns of nearly 6,000 IT professionals around the globe.

Spearline Testing
JANUARY 7, 2021
He says this is why it would also suit every company, organization, and government entity to have a disaster recovery plan, stating: “Disaster recovery planning has to remain a central part of IT management.

CIO Business Intelligence
SEPTEMBER 21, 2023
Interconnectivity of gaming systems have physically transitioned from serial-based connectivity to Ethernet-based standards over the years, allowing potential hackers easier access to the gaming and/or corporate network. Read on for his thoughts on AI, zero trust, and more. What’s on your data dashboard as the most important metrics?

CTOvision
NOVEMBER 21, 2016
We all know the expected benefits: reduction in CAPEX, better utilization of resources, improved system availability, better disaster recovery, and flexibility of compute and storage resources. The move toward cloud computing as a technology design style continues to accelerate.
Dataconomy
MAY 13, 2024
The order details need to be instantly reflected in the inventory management system located in Asia. Disaster recovery: Replicated data serves as a readily available backup, facilitating faster recovery in case of natural disasters or unforeseen technical issues and minimizing data loss and operational disruptions.

CIO Business Intelligence
DECEMBER 22, 2023
Cloud systems administrator Cloud systems administrators are charged with overseeing the general maintenance and management of cloud infrastructure. Role growth: 27% of companies have added cloud systems admin roles as part of their cloud investments.

CTOvision
FEBRUARY 22, 2017
This article increases awareness for organizations seeking to enhance their digital risk posture against the increasing threat of ransomware (a type of malware) deployed by threat actors to prevent or limit users from accessing their system until a ransom is paid.

SecureWorld News
DECEMBER 5, 2023
part 748, defines a 'cyber incident' as 'an occurrence that actually or imminently jeopardizes, without lawful authority, the integrity, confidentiality, or availability of information on an information system or actually or imminently jeopardizes, without lawful authority, an information system.'"

Kitaboo
MAY 7, 2024
If you are looking to learn more about document security systems and the challenges it poses, you’re at the right place. Challenges in Document and Information Security Advanced Cyber Threats Insider Threats Increased Data Fragmentation and Proliferation Compliance and Regulatory Requirements Legacy Systems and Technologies V.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content