Eating Our Own Zero Trust Dog Food
Forrester IT
FEBRUARY 1, 2019
It is high time for Forrester to demonstrate Zero Trust in a practical application scenario, our upcoming virtual reference architecture project aims to do just that.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Forrester IT
FEBRUARY 1, 2019
It is high time for Forrester to demonstrate Zero Trust in a practical application scenario, our upcoming virtual reference architecture project aims to do just that.
Kitaboo
MARCH 30, 2023
Although the education sector is vastly defined by legacy systems, new-age AI tools, VR (virtual reality), and augmented reality in education can bring phenomenal change in terms of automation and closing the widening knowledge gaps that exist across traditional grade systems. Let’s begin.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Forrester IT
MAY 18, 2016
Reference design for headset and controller. Google also announced a reference design for both a headset and a controller (see photo). Applications and Google Play distribution. Additionally, Android N will include a number of VR-specific performance optimization features.

CIO Business Intelligence
APRIL 25, 2024
The zero-copy pattern helps customers map the data from external platforms into the Salesforce metadata model, providing a virtual object definition for that object. “It Zero-copy integration means teams access data where it lives, through queries or by virtually accessing the file. You can do flows and automations on it.

Scott Lowe
AUGUST 16, 2017
This post provides an extremely basic “quick reference” to some commonly-used AWS CLI commands. It’s not intended to be a deep dive, nor is it intended to serve as any sort of comprehensive reference (the AWS CLI docs nicely fill that need). Refer to the Amazon ECS documentation for more details. ImageId'.

Storage IO Blog
AUGUST 17, 2017
Need to learn more about Microsoft Azure Cloud Software Defined Data Infrastructure topics including reference architecture among other resources for various application workloads? Microsoft Azure has an architecture and resources page (here) that includes various application workload reference tools.

Scott Lowe
JANUARY 19, 2024
A set of vulnerabilities in the open source reference implementation of the UEFI specification has been uncovered. The flaws, referred to as PixieFail, specifically affect the PXE network boot process. Operating Systems/Applications Julia Evans has a lovely article on Git commits that is well worth reading.

Dataconomy
NOVEMBER 24, 2023
In the rapidly evolving realm of gaming, applications, and virtual reality, Ready Player Me has emerged as a transformative force, offering a gateway into a world of immersive experiences. Full-body avatars, complete with intricate rigging and animation, represent an entire person in the virtual world.

Scott Lowe
SEPTEMBER 11, 2013
This is session EDCS008, “Virtualizing the Network to Enable a Software-Defined Infrastructure (SDI).” Brian starts the session with a review of how the data center has evolved over the last 10 years or so, driven by the widespread adoption of compute virtualization, increased CPU capacity, and the adoption of 10Gb Ethernet.

CIO Business Intelligence
DECEMBER 7, 2022
The open architecture, which is sometimes referred to as fog computing, drives storage and data processing towards a location where it’s needed. NTT manages the hardware, application deployment, security and software patching. These technologies require features that are enabled through NTT’s Edge as a Service,” says Sandhu.

Cloud Musings
JANUARY 26, 2012
NJVC® and Virtual Global Announce Release of PaaS White Paper: Paper Clarifies the Confusion Surrounding PaaS for Federal IT Buyers—Why It Is Important and How It Can Cut Development Costs by 50 Percent. GovCloud Daily. GovCloud Presentations. GovCloud on Facebook. Get "Cloud Musings" by RSS. Thursday, January 26, 2012. VIENNA, Va.,

SecureWorld News
APRIL 9, 2023
The browser isolation technique considers non-whitelisted websites unreliable and isolates them from the local machine in a virtual environment. A non-signature method for preventing web threats, referred to as Browser Isolation or remote browsing, has been introduced to securely present web pages without affecting the user's experience.

Scott Lowe
DECEMBER 31, 2021
Kevin Swiber shows how to use Postman to deploy an application onto a Kubernetes cluster. Operating Systems/Applications. Beth Marshall (aka “Beth the Tester”) provides a reference guide to blocks in Postman Flows. LaunchBar is, in my opinion, an extremely useful macOS application. Virtualization.

CIO Business Intelligence
DECEMBER 6, 2022
The open architecture, which is sometimes referred to as fog computing, drives storage and data processing towards a location where it’s needed. NTT manages the hardware, application deployment, security and software patching. These technologies require features that are enabled through NTT’s Edge as a Service,” says Sandhu.

Scott Lowe
JANUARY 5, 2024
Operating Systems/Applications Nick Janetakis shares another tip for determining how long a Docker container was running. Although this article references additional posts, it doesn’t appear that any more posts on this topic have been published (yet). Nisar Ahmad explores whether Terraform or Pulumi is better for your use case.

SecureWorld News
DECEMBER 8, 2021
Mandiant refers to the threat actors as "one of the toughest actors we have encountered." Use of accounts with Application Impersonation privileges to harvest sensitive mail data since Q1 2021.". Use of credentials likely obtained from an info-stealer malware campaign by a third-party actor to gain initial access to organizations.".

CIO Business Intelligence
MAY 18, 2022
The list is growing and growing,” says Gordon Barnett, principal analyst at Forrester, “moving away from EA that just looks at applications and infrastructure to be truly enterprise. That may require, for example, an analysis of ERP systems to understand all the dependencies and functions that reference a bill of materials, he says.

Kitaboo
JANUARY 31, 2023
Benefits of White Labeling Your E-Learning Courses Brand Reflection Cost and Time Saving Increased User-Engagement Easy Market Expansion Seamless Integration With Other Applications Key Metrics Measurement 3. Schools, colleges, and universities are increasingly hosting virtual classes with the help of eLearning materials.

CTOvision
DECEMBER 17, 2013
By Prayson Pate Openness is one of the most-cited advantages of cloud-based applications, Software-Defined Networking (SDN) and Network Functions Virtualization (NFV). For example, a proprietary application like an email program might have application programming interfaces (APIs) that allow another application to send an email.
TM Forum
SEPTEMBER 20, 2021
The digital twin approach enables collaboration between partners involved in smart city planning, application development and construction, but there are challenges in implementing a digital twin-based smart city. Collaborating with industry stakeholders to build digital twins of physical entities and applications. external_url.

CIO Business Intelligence
FEBRUARY 14, 2023
Kevin Grayling, CIO, Florida Crystals Florida Crystals It’s ASR that had the more modern SAP installation, S/4HANA 1709, running in a virtual private cloud hosted by Virtustream, while its parent languished on SAP Business Suite. Reference implementation Grayling reached out to his network to identify an implementation partner.

Flexagon
JULY 28, 2022
Along with this, it provides comprehensive integration support for a multitude of middleware platforms, third-party tools, and packaged applications. Endpoints are the FlexDeploy representation of a device or virtual machine where the operations can be run. SCP commonly refers to both the Secure Copy Protocol and the program itself.

CIO Business Intelligence
JULY 14, 2022
Infinidat added cyber resilience on its InfiniGuard ® secondary storage system during the past year and, at the end of April 2022, across its primary storage platforms with the InfiniSafe Reference Architecture, encompassing Infinidat’s complete portfolio. The need for the lowest latency while delivering the highest application performance.

Cloud Musings
NOVEMBER 20, 2016
In cloud computing, interoperability generally refers to the ability of service models from different cloud service providers to work together. He believes that applications can be built to be interoperable across different infrastructure platform. He believes interoperability does not necessarily start at the IaaS layer.

CIO Business Intelligence
FEBRUARY 24, 2023
The future of enterprise IT is multi-cloud — the ability to distribute applications and services across a combination of clouds. The battlefields of tomorrow are digital domains, which means the tools essential to a country’s national defense have to be both physical and virtual. Just last month, the U.S.

Fountainhead
JANUARY 19, 2012
Insights into Data Center Infrastructure, Virtualization, and Cloud Computing. In the context of data, applications and cloud computing, this question takes on a new perspective - and the role of Mohammed and the Mountain may soon reverse. But theres no denying that the application is becoming more mobile. Fountainhead.
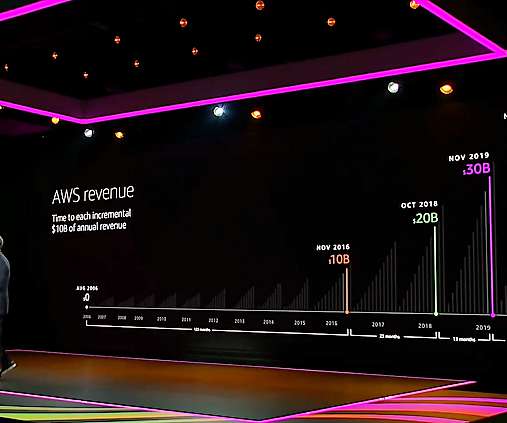
GeekWire
DECEMBER 3, 2020
Amazon Web Services CEO Andy Jassy with a chart showing AWS revenue growth at the company’s virtual re:Invent conference this week. But he sought to assure the virtual audience that AWS is not even close to its zenith, citing the 96% of the estimated $3.6 Screenshot via webcast).

CTOvision
JANUARY 26, 2016
Their products include high speed random from a quantum source, powerful key and policy management with embedded secure key store, as well as flexible encryption modules for a range of applications. However approaches are not fail safe; furthermore, once zeroized the data is permanently lost.

Network World
APRIL 4, 2017
Most organizations are pretty good at vetting job applicants up front. They interview candidates, contact references, and in many cases conduct at least rudimentary background checks to bring out any issues of concern before making a hiring decision. To read this article in full or to leave a comment, please click here

CIO Business Intelligence
JULY 5, 2023
Two decades ago, as CIO and CTO at Nationwide Insurance, he inspired colleagues to implement what were then referred to as “green initiatives,” such as printing less paper and using more efficient lightbulbs. If you’re moving to an environment where you’re not managing servers anymore, the Linux engineers need a path forward,” Koushik says.

GeekWire
FEBRUARY 4, 2023
Applications of Pattern’s technology include a rapid COVID-19 test based on patterns in light from spit, and drug combinations believed to kill breast cancer cell lines in culture. .” It’s a reference to CEOs making disproportionately large bets on technologies with limited potential.

SecureWorld News
MAY 19, 2022
The wide adoption of cloud-native applications and infrastructure has propelled DevOps and a self-service culture enabling developers to go from code to cloud in hours. Over the years, organizations have referred to this idea as a secure-by-default framework, security paved road , DevSecOps guardrails , and several other monikers.

CIO Business Intelligence
MAY 23, 2023
VMware has an amazing opportunity to further grow and scale its pioneering virtualization technology, and Broadcom is committed to innovation and building VMware’s professional services capabilities. And this is our shared goal and vision together with VMware.

Valerian Tech
JULY 10, 2023
Understanding AI and ML AI refers to the simulation of human intelligence in machines, enabling them to perform tasks that typically require human intelligence. Additionally, chatbots and virtual assistants are being employed for customer support and personalized financial advice.

Scott Lowe
DECEMBER 9, 2022
food references in the title of this article are almost too much. Operating Systems/Applications. Virtualization. But is it really a virtual machine ? These are worth a read if security and compliance are your jam (see here , here , here , here , here , here , and here ). See here for more details. The corny (cheesy?)

CIO Business Intelligence
MARCH 24, 2022
The first is to run transaction-intensive banking applications, including bank statements, deposits, mobile banking, debit-card processing, and loan payments. The second is to host mobile applications, containers, and artificial intelligence (AI) applications — what Sonnenstein calls “acting as a full-fledged member of the modern universe.”.

CIO Business Intelligence
MARCH 24, 2023
The Business Application Research Center (BARC) warns that data governance is a highly complex, ongoing program, not a “big bang initiative,” and it runs the risk of participants losing trust and interest over time. As a practice, it is about establishing systematic, formal control over these processes and responsibilities.

Storage IO Blog
JANUARY 31, 2015
Having insight and awareness into how your environment along with applications is important to know to focus resources. Also keep in mind that a bit of flash SSD or DRAM cache in the applicable place can go along way while a lot of cache will also cost you cash.

GeekWire
JULY 17, 2023
” NFTs, sometimes referred to as digital collectibles, are digital certificates of ownership that use blockchain technology and cryptocurrency. ng Collectable, consumers gain exclusive access to digital content like videos, MP3 files and virtual concerts. ng Collectables.” By owning a S!ng

CIO Business Intelligence
APRIL 18, 2023
Other responsibilities may include addressing digital transformation initiatives, guiding application development, and identifying security issues. What is a virtual CIO versus a fractional CIO? A fractional CIO brought into an enterprise to guide a relatively minor task or project is sometimes referred to as a virtual CIO, or vCIO.

Kitaboo
JANUARY 15, 2024
Modern and innovative technology integration in education refers to the use of technology to enhance the student learning experience and achieve respective learning goals. These applications also help educators keep everything organized and arranged to enable higher-ed students to be more involved in their learning.

Kitaboo
MARCH 17, 2023
The Importance of Compatibility in K12 Digital Publishing Compatibility in online education refers to the ability of a resource to be accessed across different platforms and devices, such as cross-platform readers. Advocacy for Inclusion: This refers to how inclusive the material is. Why inclusion is important is also explained.

Dataconomy
AUGUST 11, 2023
You will be astonished by the selection of sports applications available when you visit the Apple App Store and Google Play Store. Or we can refer to other teams. Apps for fantasy sports The following of these applications is widespread around the world. These professionals can help you with development: [link].

CIO Business Intelligence
OCTOBER 13, 2023
AI researcher AI is new territory for businesses, and there’s still a lot to discover about the technology, which is why they’re looking to hire AI researchers to help identify the best possible applications of AI within the business.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content