Hacker Group Claims Extraordinary Access to User Authentication Firm Okta
Gizmodo
MARCH 22, 2022
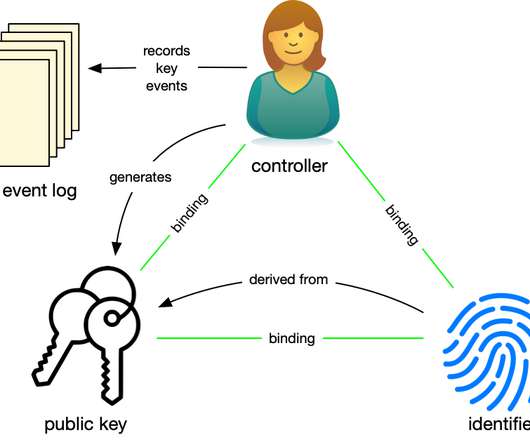
Hacker group LAPSUS$ posted images on its Telegram channel overnight claiming it achieved administrator access to Okta, a user authentication and data management company. And if that’s true, it’s potentially bad for a number of large firms that use Okta services. Read more.

















































Let's personalize your content