Passkeys: Using FIDO for Secure and Easy Authentication
Phil Windley
MARCH 27, 2023
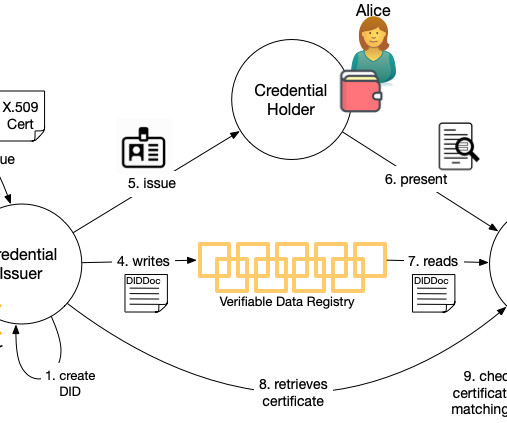
Summary: Passkeys, the popular name for FIDO, are not only easy, they offer better protection against phishing than other forms of multi-factor authentication. She's a security expert and focused many of her remarks on the relative security of different multi-factor authentication (MFA) techniques, a topic I cover in my book as well.














































Let's personalize your content