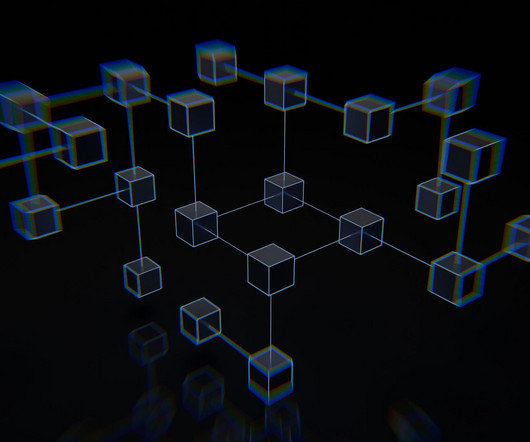
FCC proposes BGP security measures
Network World
MAY 17, 2024
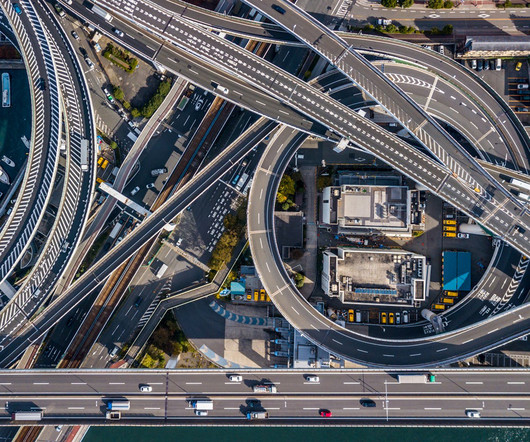
Jessica Rosenworcel wants ISPs to tell her how they’re securing BGP (Border Gateway Protocol) , a critical system for routing internet traffic. The proposal aims to protect against bad actors who could pose a threat to national security and disrupt critical Internet infrastructure by exploiting BGP vulnerabilities, the FCC said Wednesday.











































Let's personalize your content